It’s time we understand the view that “Every Attacker Leverages a Weakness.” Understanding this view shifts how we approach exposure management; otherwise, organizations will be prone to cyberattacks. We MUST actively seek out these weaknesses and gain a deeper understanding of our IT infrastructure.
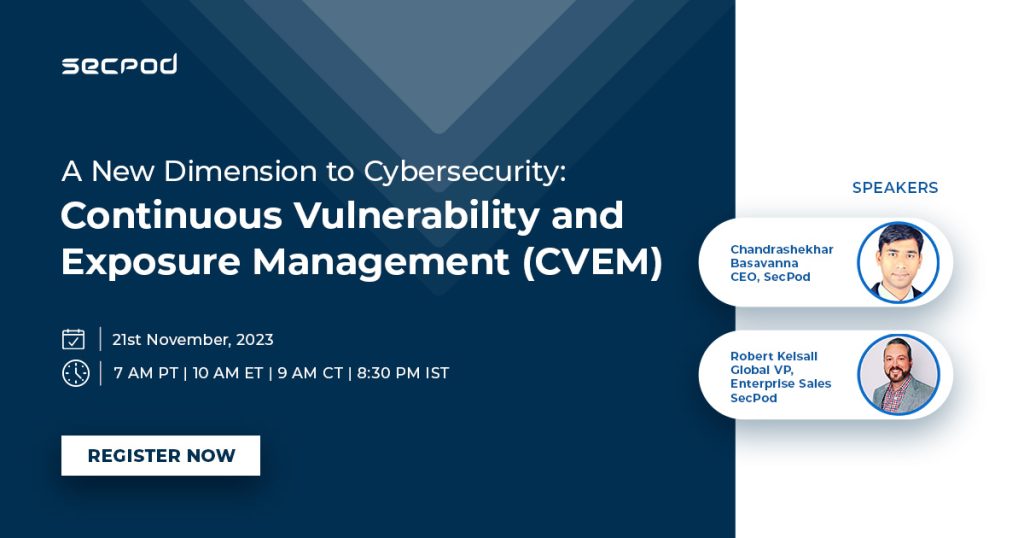
This approach leads us to go beyond exposure management, i.e., continuous vulnerability exposure management (CVEM). How do we start implementing this approach? And start rethinking cybersecurity from a ‘weakness’ angle? Join us in our live webinar where we discuss:
- Are vulnerabilities and exposures the same?
- Are there vulnerabilities beyond ‘software vulnerability’ that we must pay attention to
- What is ‘Management’ when it doesn’t include remediation or mitigation? Shouldn’t vulnerability, exposure, or weakness management
- ‘Continuous’ as well?


