Seamlessly orchestrate and automate healthy cyber hygiene measures
Security and Endpoint Management to Ensure Seamless Cyber Hygiene Automation
Implement a Robust Security Strategy With a Single, Cloud-Native Console
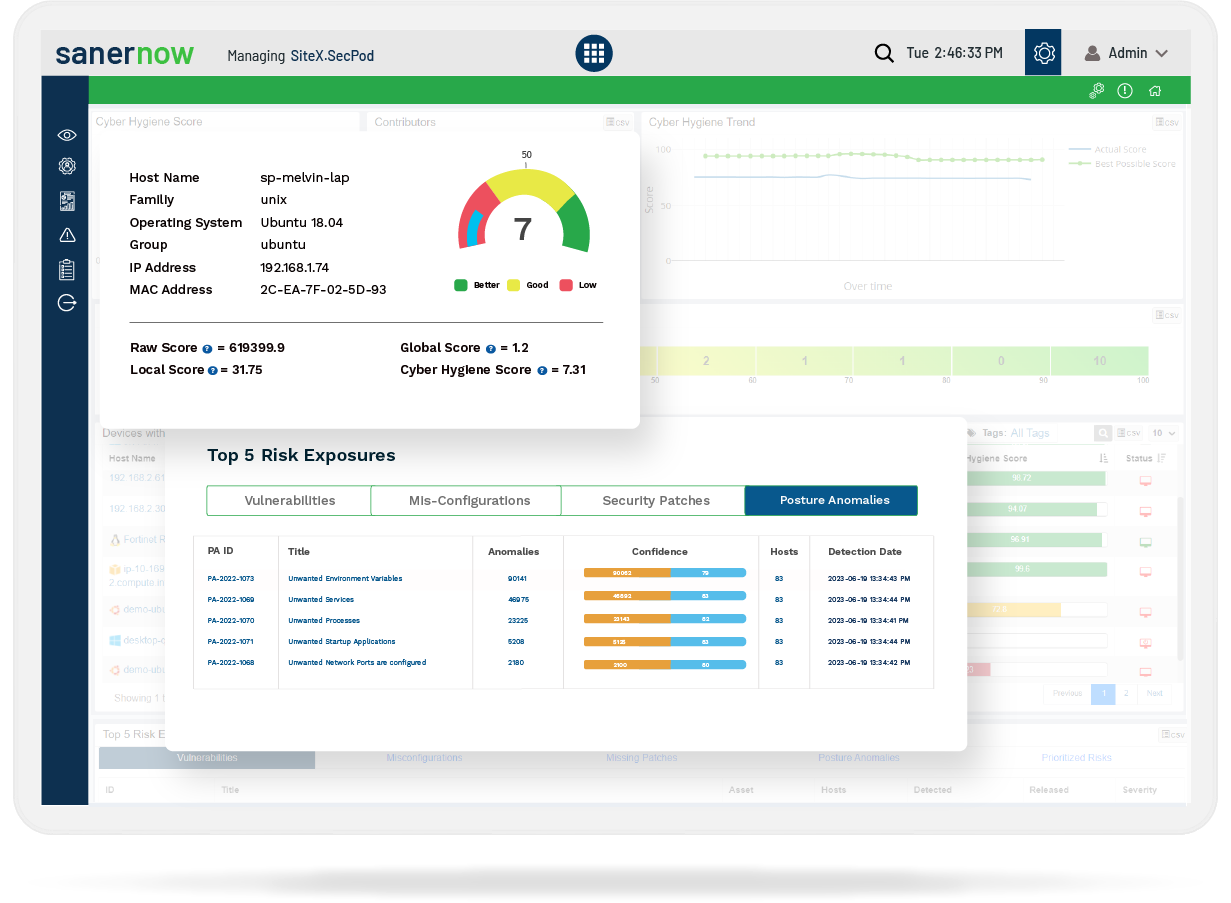
Take a unified approach to effectively implement a cyber hygiene routine with a single point of control across your enterprise devices. Reduce your attack surface and safeguard your network devices from potential security breaches with cyber hygiene automation.
Reduce the Complexities of Using Multiple Point Solutions
Eliminate the overlaps and false positives of using swivel chair interfaces to implement different operations of cyber hygiene by using our integrated, one-point approach. Seamlessly perform risk assessment and mitigation in your network without switching between screens.
Orchestrate all Cyberhygiene Routines Using One Powerful, Multifunctional Agent
Use our light-weight, easily-deployable, powerful, multifunctional agent to remotely perform all required cyber hygiene operations across your devices. With this single point of control, continuously monitor your risk exposure, assess, and remediate them instantly.
Boost Productivity and Save Time Using Cyber Hygiene Automation Techniques
Wide Range of Capabilities to Secure and Manage Devices Proactively
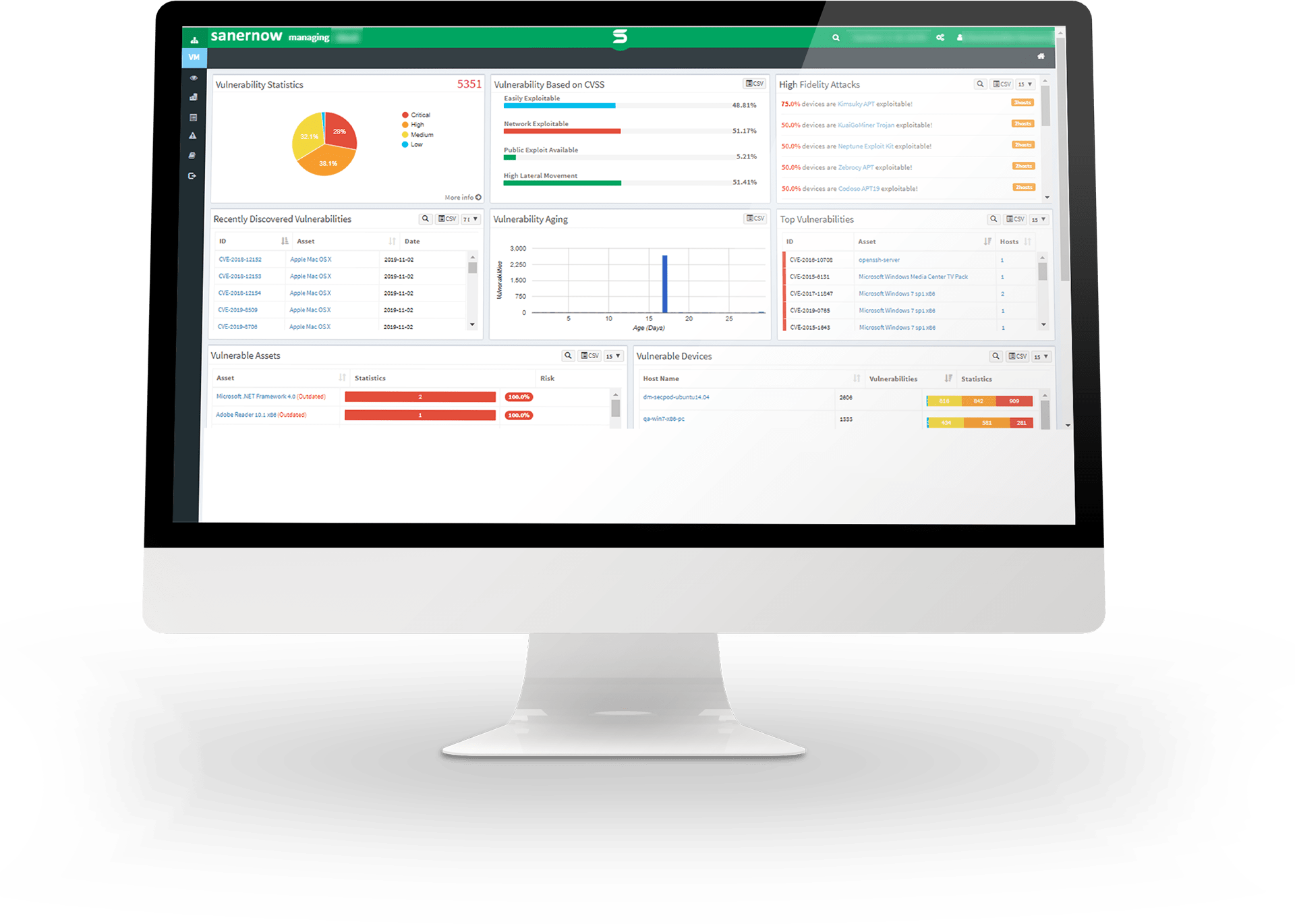
Run Rapid and Continuous Vulnerability Scans in Less than 5 Minutes
Scan and detect the vulnerabilities in your devices in less than 5 minutes, with SanerNow’s efficient scanning algorithm. Run an always-on vulnerability management program to gain real-time visibility and control over your attack surface.
Discover your Device Vulnerabilities Accurately with 175,000+ Vulnerability Checks
Leverage our industry renowned SCAP feed with over 175,000 vulnerability checks and 400-500 configuration checks per OS, to precisely discover your device vulnerabilities and analyze your cyber risk accurately.
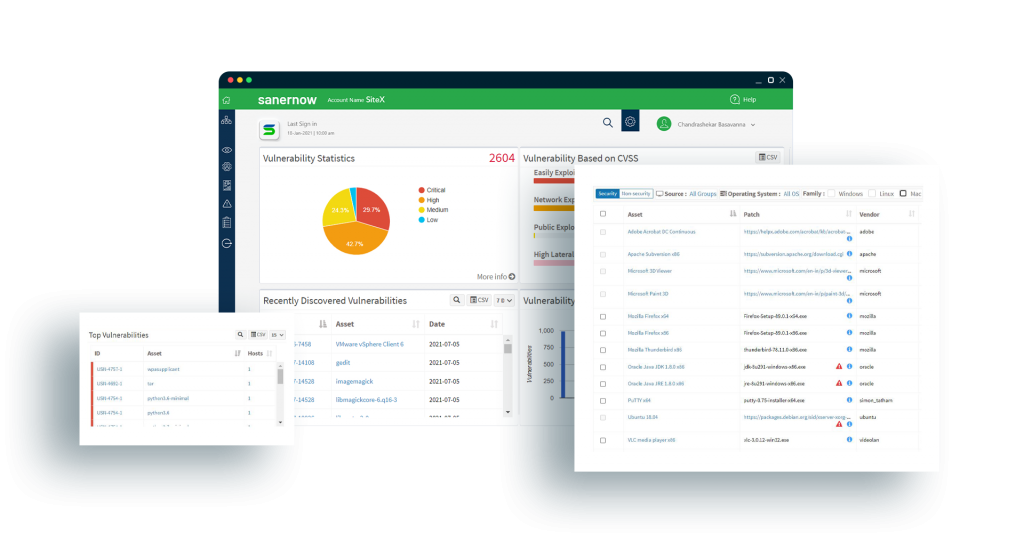
Reduce Risk Exposure with Integrated and Automated Patch Management
Analyze Exploit Potential and Prioritize Vulnerabilities Based on Risk
Use SanerNow to thoroughly assess identified vulnerabilities and prioritize them based on their severity level using live metrics beyond CVSS scores. Improve your security posture, analyze your device vulnerabilities, assess your threat surface and mitigate risks.
Firmware Patches for Truly Complete Risk Mitigation
Comprehensive set of patches that cover software as well as firmware across all nodes to reduce vulnerabilities and security risks to your organization.
Gain Continuous Visibility over IT Assets, Blacklist, and Whitelist Applications
Continuously perform real-time IT asset monitoring, detect vulnerable applications and blacklist or whitelist them accordingly. SanerNow displays a list of rarely used and outdated applications to help you optimize IT spend and remove rogue applications.
Monitor 100+ Metrics and Keep your Devices Healthy
Continuously track and monitor all your devices, with stringent and regular security checks. Monitor antivirus deployments, status of important system services and files, registry keys, rogue processes, etc., to harden your system configurations and keep your devices healthy.
Apply Strong Security Controls and Strengthen your Device Security Posture
Tighten the security across your devices and execute strong security measures, including enabling firewall policies and other security checks, quarantining or isolating necessary devices or networks, discovering, and protecting sensitive data, etc.
Block Malicious Applications and Devices, Reduce Attack Surface Instantly
Block any suspicious or malicious or unwanted applications and devices on your network. Implement effective application and device control across your devices and prevent security breaches to safeguard your network from emerging cyberattacks.
Regulate and Remediate your Security Compliance Requirements
SanerNow supports major security standards such as HIPAA, PCI, ISO, NIST 800-53, and NIST 800-171 right out-of-the-box, along with the ability to create custom policies. Harden your system configurations, demonstrate security compliance to industry and organizational standards.
Effectively CyberHygienize Your Devices Now
Get 1-month free unlimited access and try it yourself.