Integrated Vulnerability and Patch Management
Actively scan, detect, assess, prioritize, and remediate vulnerabilities in the same console
Get all Patching and Vulnerability Management Controls in One Place
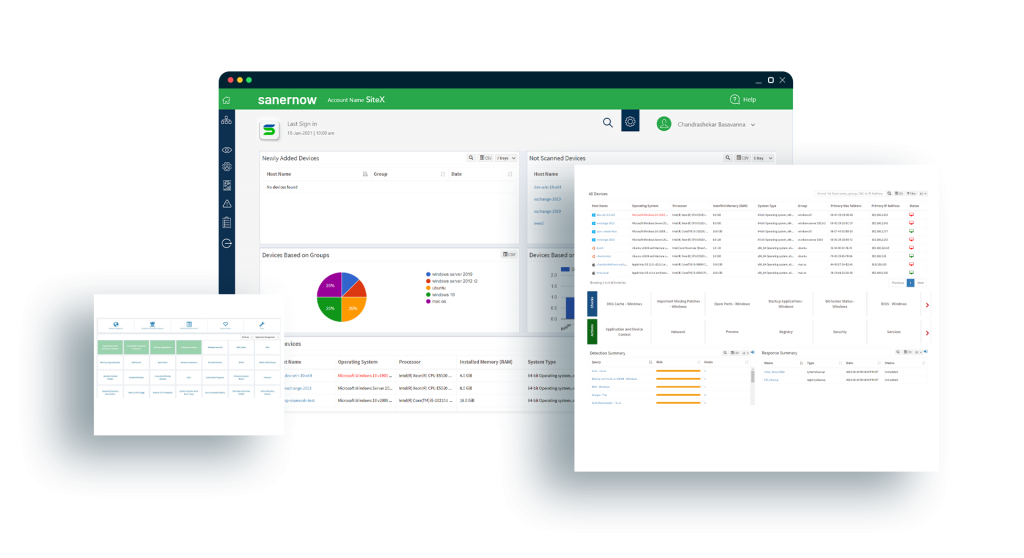
Execute the Complete Cycle from Scanning to Remediation in One Cloud-Based Console
Get all scanning and vulnerability remediation tools in one unified cloud-based console. You can do detection and vulnerability remediation remotely with ease.
Leverage the World’s Largest Vulnerability Intelligence Feed with 175,000+ Security Checks
SecPod hosts the world’s largest SCAP vulnerability database with over 175,000 security checks and vulnerabilities. With the best database to detect security risks, your security posture increases multifold.
Orchestrate all Cyberhygiene Routines Using One Powerful, Multifunctional Agent
Automate the Entire Patching and Vulnerability Management Workflow
SanerNow runs automatic vulnerability scans according to your schedule. It also supports end-to-end automation for patching Windows, MAC, Linux, and 450+ third-party applications.
Detect and Remediate a Vulnerability from the Same Console
Perform Rapid and Continuous Vulnerability Scans
Scan and detect the vulnerabilities in your devices in less than 5 minutes with SanerNow’s intelligent scanning algorithm.
Execute all Patching and Vulnerability Management with Intelligent Multi-Functional Agents
Use the lightweight, powerful, and multi-functional agents installed in your devices to perform all tasks from scanning up to remediation.
Leverage Perimeter-Less Cloud-Based Management
Efficiently manage vulnerabilities and patches across your remote workforce with a single, centralized, cloud-based console.
Get Accurate Prioritization with High-Risk Vulnerability Identification
Use SanerNow to thoroughly identify vulnerabilities and prioritize them based on their severity level going beyond just CVSS scores.
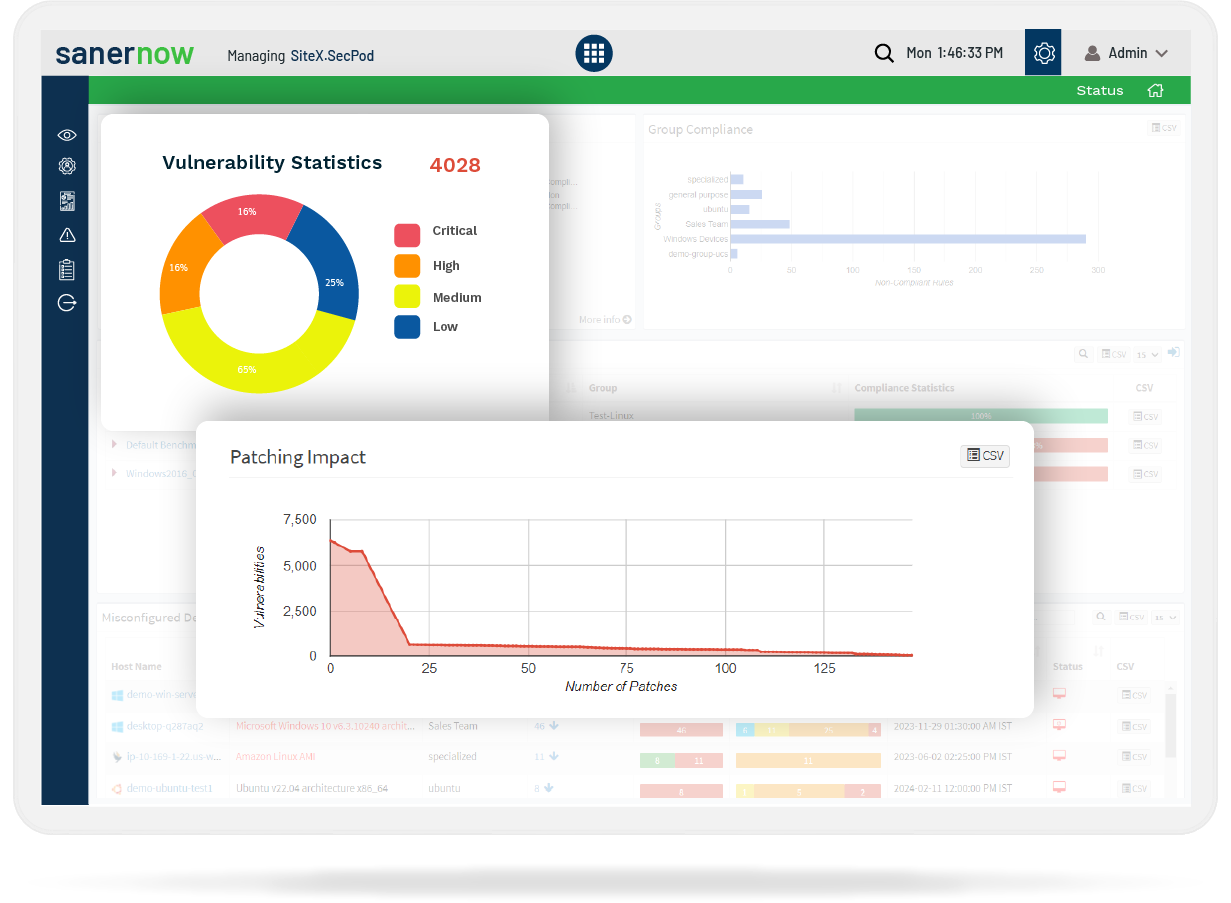
Automated and Integrated Patch Management
Instant software vulnerability remediation using an automated and integrated patch management approach. Eliminate the complexities of using swivel chair interfaces to execute different vulnerability management tasks using in-built vulnerability remediation tools.
Get Seamless Cross-Platform and Third-Party Applications Patching with Quick Support for Latest Patches
Get the latest patches for all three operating systems (Windows, Mac, Linux) and 450+ commonly used third-party applications. All within 24 hours of patch release by the vendor.
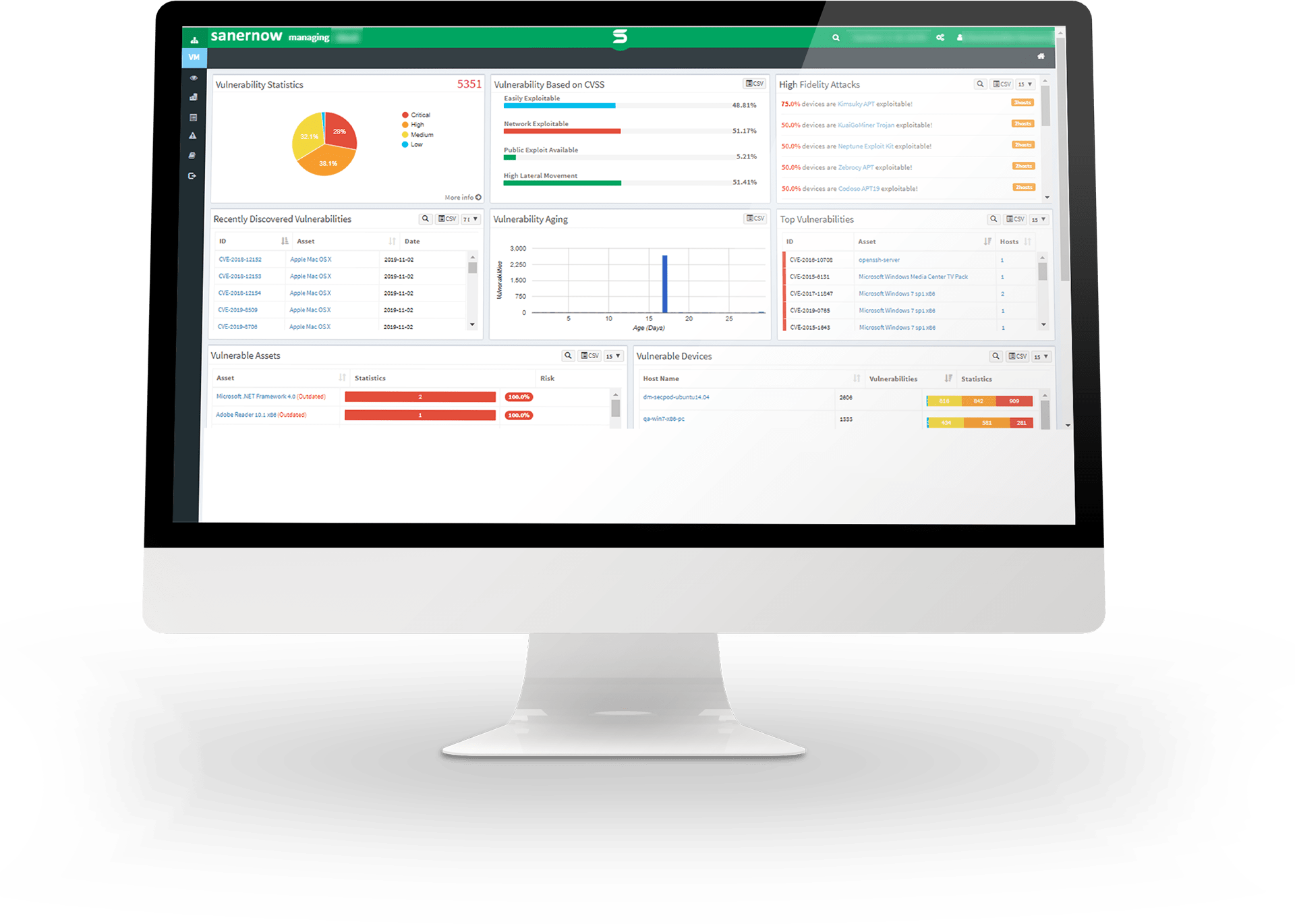
Implement 360-Degree Security Posture Visibility with Unified Insightful Dashboards
Experience the ease of risk discovery based on severity, age, device type, and exploit potential level with SanerNow’s continuous vulnerability management. Stay ahead of the threat curve, view, and eliminate risks with SanerNow’s comprehensive and actionable dashboard.
Ensure Zero-Disruption Patching with Pre-Tested and Verified Patches, with Ability to Rollback
SanerNow can test patches on customized test groups before deploying them to devices on the entire network. Uninstall faulty patches with a handy rollback feature to guarantee near-zero downtime.
Effectively Patch Your Vulnerabilities Now
Get free unlimited access and try it yourself.