Patch Management Process
Patch Management Process
Before you start patching, it is good to have a strategic approach for applying patches rather than just deploying without knowing the impact. Every patch management tool will have a detailed step-by-step patch management process. It should be implemented in such a way that it is both cost-effective and security-focused.
The 8-step patch management process
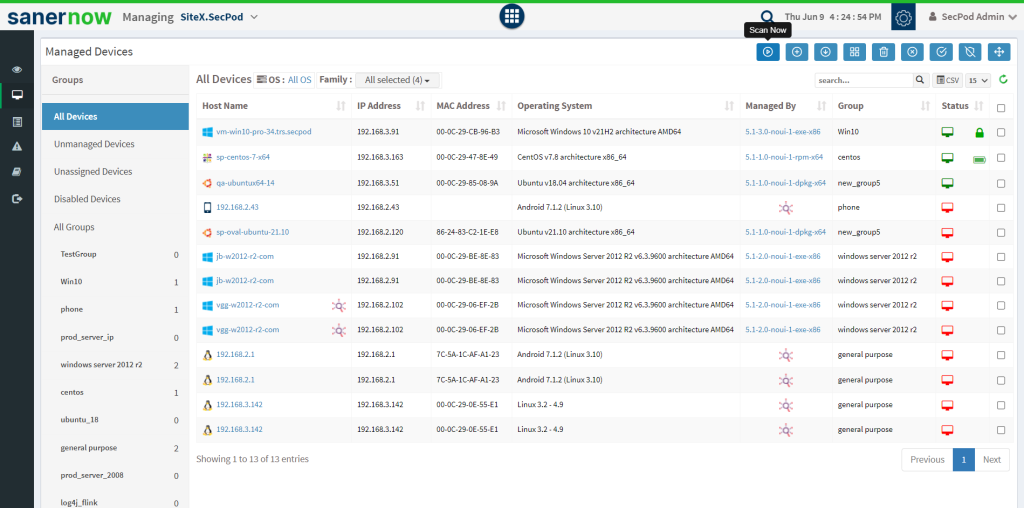
1. Gain visibility into asset inventory: IT assets information would be stored in different formats say spreadsheets, word, databases, and more it would take a lot of resources to bring them all together in one place. It is essential to have detailed information about your organization’s assets together; this would help the patch management software to easily find and install patches more accurately.
2. Detect missing patches: It is a foundational step in the patch management process. Complete network scanning to detect all the missing non-security and security patches.
3. Download patches from vendors: Vendors release patches every day. Once you are aware of the latest patches, download them from their respective vendors and have a database where you can store and access these patches for deployment.
4. Prioritize patches: After detecting patches, you might encounter hundreds of patches that need to be deployed. Assess and prioritize these patches based on their severity level with a patch manager to first address the most critical ones, followed by less critical ones.
5. Test Patches: Create a test environment where you can deploy the patches and test if any issue would cause software malfunction and downtime and affect the day-to-day activities.
6. Deploy patches on live environment: After patches are tested and are ready to be deployed in an actual live environment, schedule and deploy patches across your organization’s devices.
7. Perform patch audit: Few patches would have failed during the patching process, and it might need a patch rollback. So, performing a patch audit with a patch management tool would be essential to see if they are working fine.
8. Update the patch report: During analysis or auditing, have a patch report showcasing deployed patch version and the time taken to deploy a particular patch or patch that failed will be helpful.

Security Patch Management
It is a process of deploying patches that helps solve code vulnerabilities or errors across your organization’s network.
Security patches are updates of correcting software code errors; this helps keep your devices secure and safe from attacks. There are non-security patches that focus on feature enhancement or include a few minor changes.
A security patch management process typically includes
- Identifying software or assets that poses a security risk
- Maintaining an up-to-date patch repository.
- Assessing and testing patches to ensure they perform correctly
- Deploying patches and making sure no other updates are missing
SanerNow Patch Management
SanerNow patch management software is an end-to-end and automated patch management software. It performs everything from scanning, deployment, and reporting from a single console.
It has the world’s largest SCAP repository with over 175,000+ checks. SanerNow supports all major OSs and 450+ third-party applications.
How SanerNow Performs Patch Management:
After performing scans on all IT assets and their networks, the final analyzed report helps to prioritize vulnerabilities. The process ranges from the complexity of the environment to various available IT security data points. Some of them are as follows:
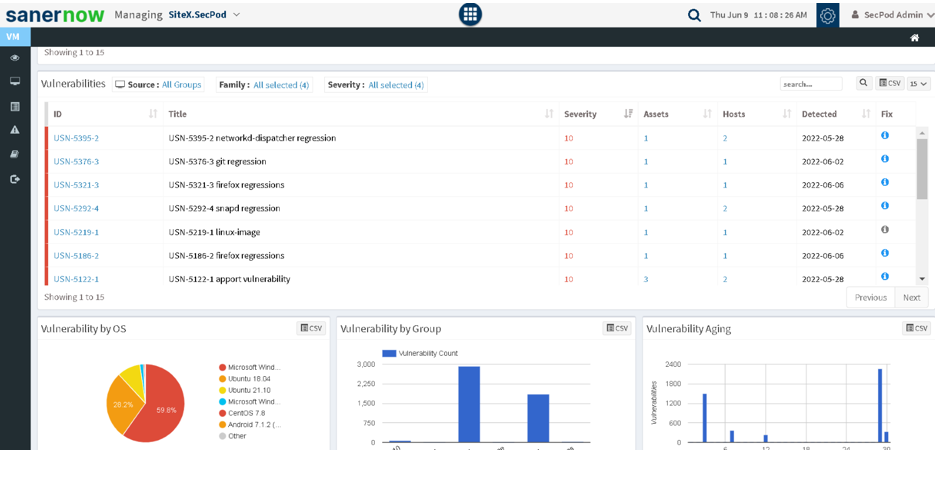
Step 1: Scan and Detect missing patches:
SanerNow runs the industry’s fastest scans in 5 minutes. SanerNow’s vulnerability management tool scans through all your IT assets and lists all the missing patches and vulnerabilities present in your IT environment, and suggests appropriate patches to remediate the vulnerabilities.
Step 2: Assess and prioritize patches:
After the scan, SanerNow lists all patches. Patch management for Windows, are directly accessed from the WSUS server, Linux and macOS patches would be directly accessed from their vendors.
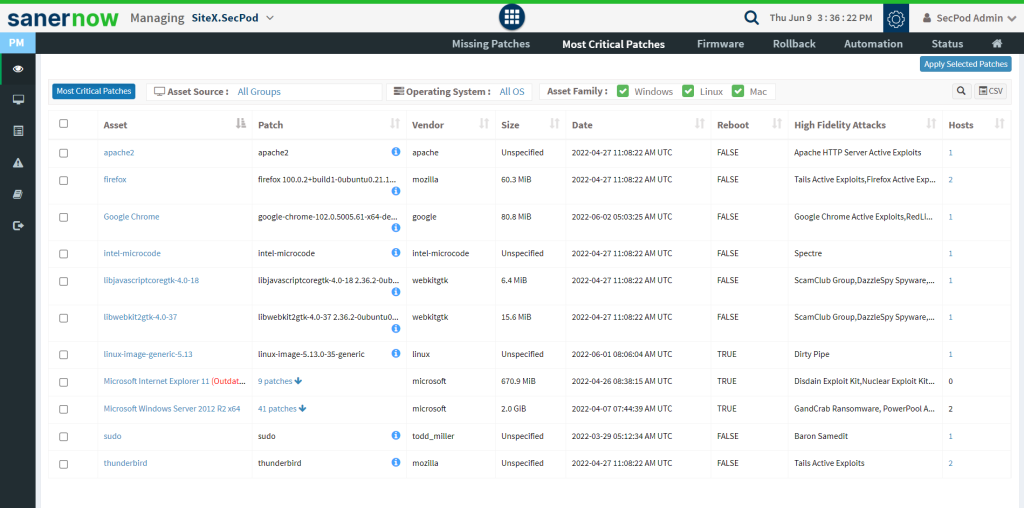
For third-party applications, patches would be downloaded, pre-tested, and are stored in the in-built patch repository, and would be ready for deployment.
While scanning for vulnerabilities, you will come across many patches, and prioritizing them would come in handy. SanerNow automatically prioritizes patches based on severity and CVSS scores has critical and less critical patches. During deployment, address the most critical patches first followed by less critical patches.
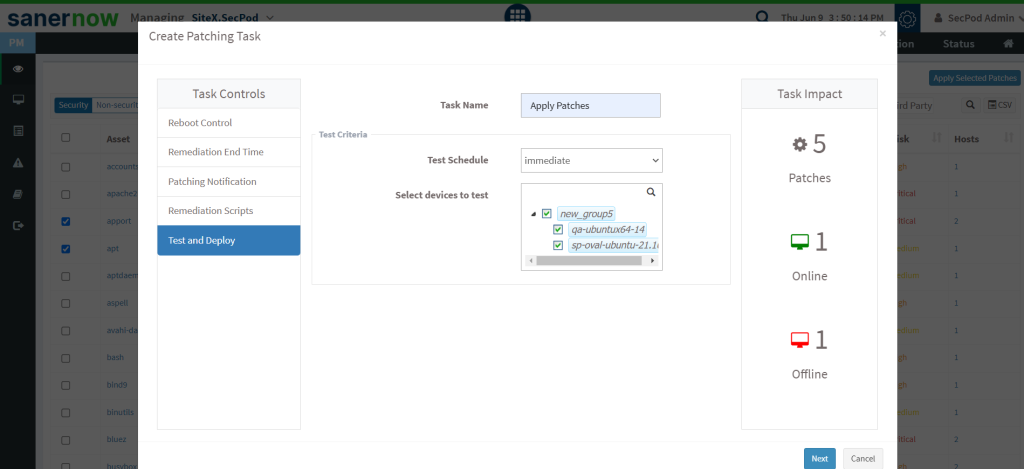
Step 3: Test and Approve patches
During a few circumstances, patches would cause system malfunction, errors, or interrupt day-to-day activities. Therefore, SanerNow patch management software allows you to test the security patches in your non-production environment, see if it encounters any issues, and then deploy them in your live environment.
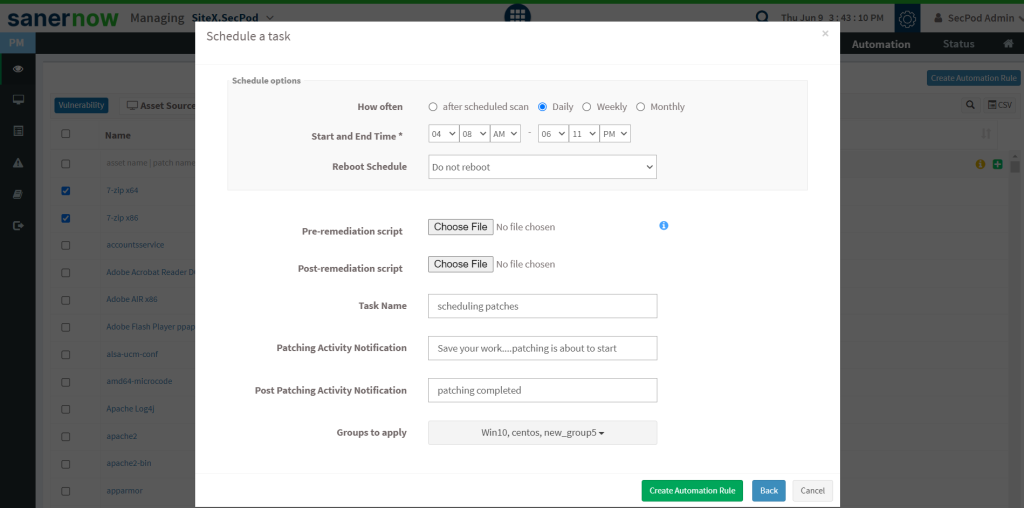
Step 4: Deploy Automatically
You can schedule your patches for automatic patching. SanerNow can schedule patching either daily, monthly, or weekly basis, and the timing of your scans can be chosen according to your convenience with its patch management tool.
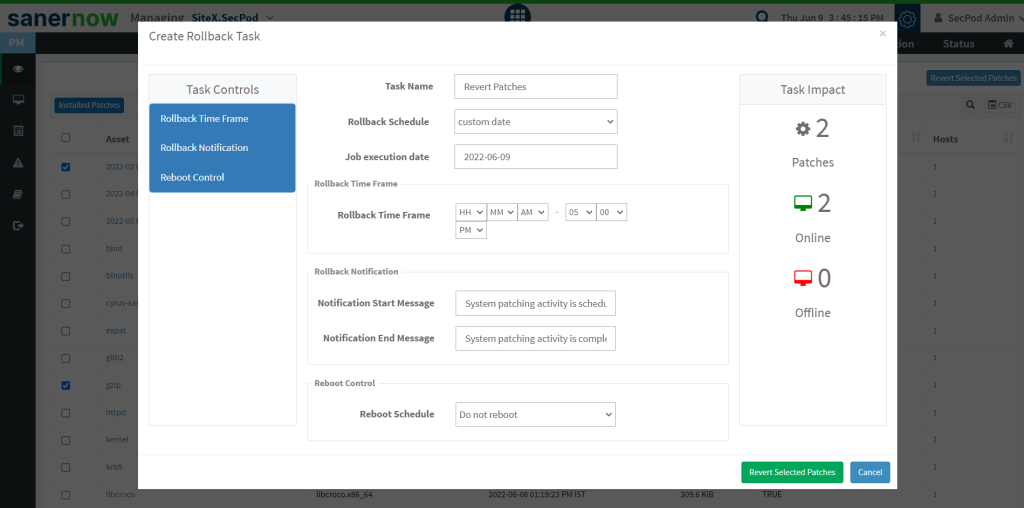
SanerNow’s patch rollback can be used when you want to go back to the application’s previous version.
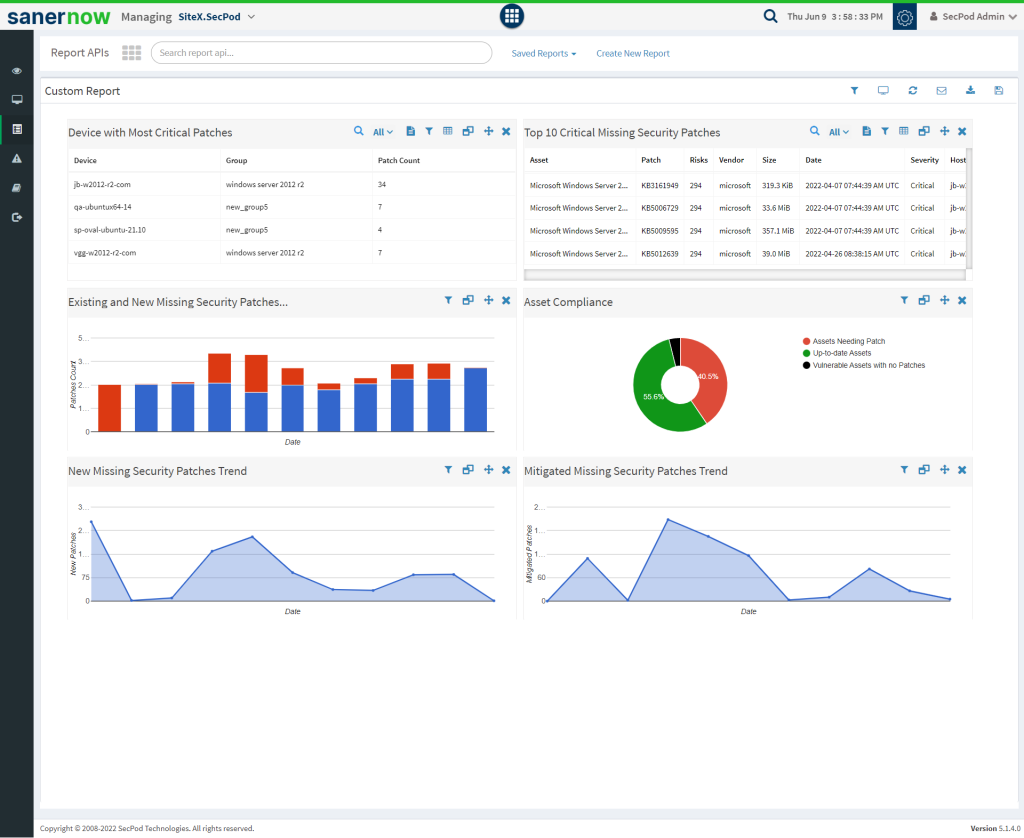
Step 5: Report
In the time of analysis, reports play a vital role. With reports, you will have information on patches deployed, version of the patch, patch that failed, devices with critical missing security patches, and more.
SanerNow patch management software supports 450+ reports, canned, and can be customized according to your requirements.