Saner CVEM Solution for
Risk-based Vulnerability Management
To discover, normalize, classify and prioritize risks



SecPod's Saner CVEM is an Ideal Compliance Management Tool

Saner CVEM is a compliance management
tool. It ensures our team and staff members are security compliant, aware, and
up-to-date. Saner CVEM is an effective tool for detecting non-complying devices
or personnel while enforcing compliance regulations and industry-specific
standards on them. SecPod’s Saner CVEM solution ensures there’s no getting away
with ill-advised security moves.
Assistant Banking Officer
30B+ USD Firm
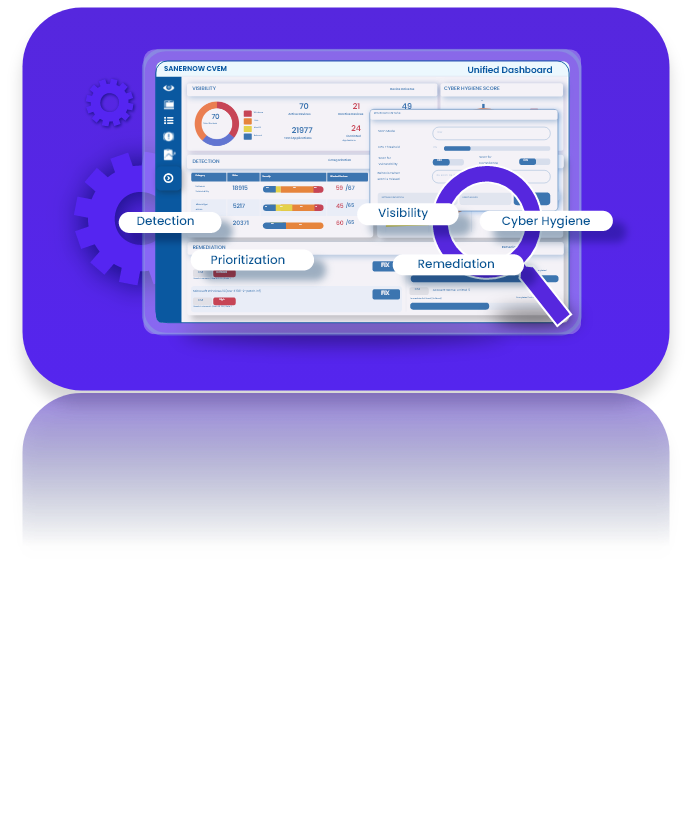
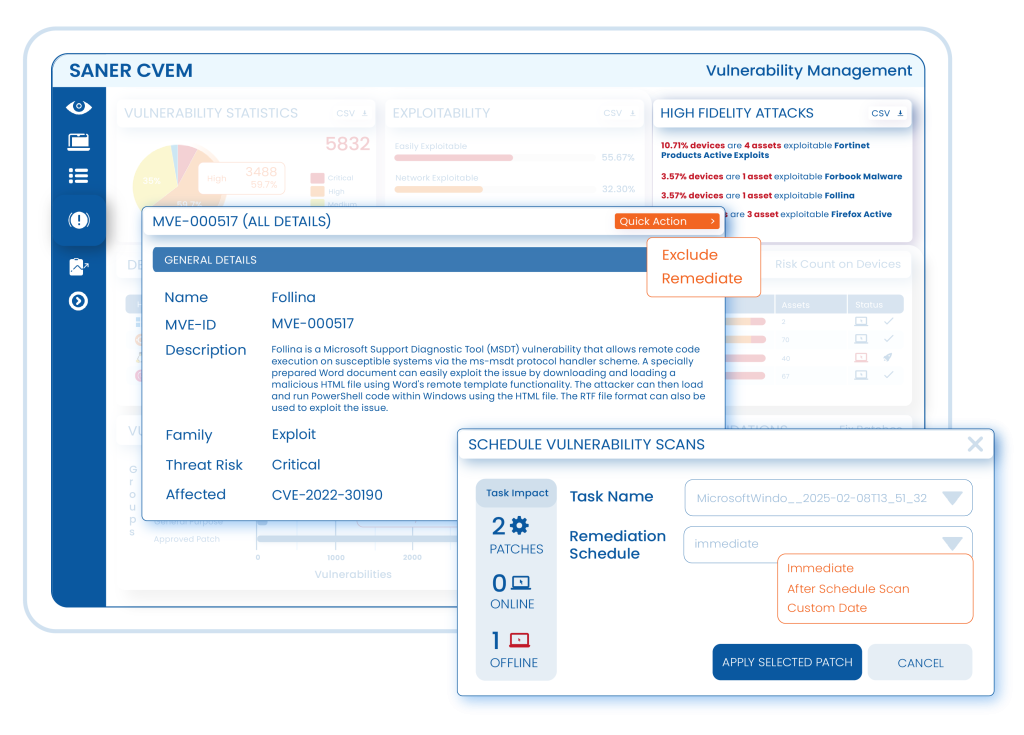
SANER CVEM
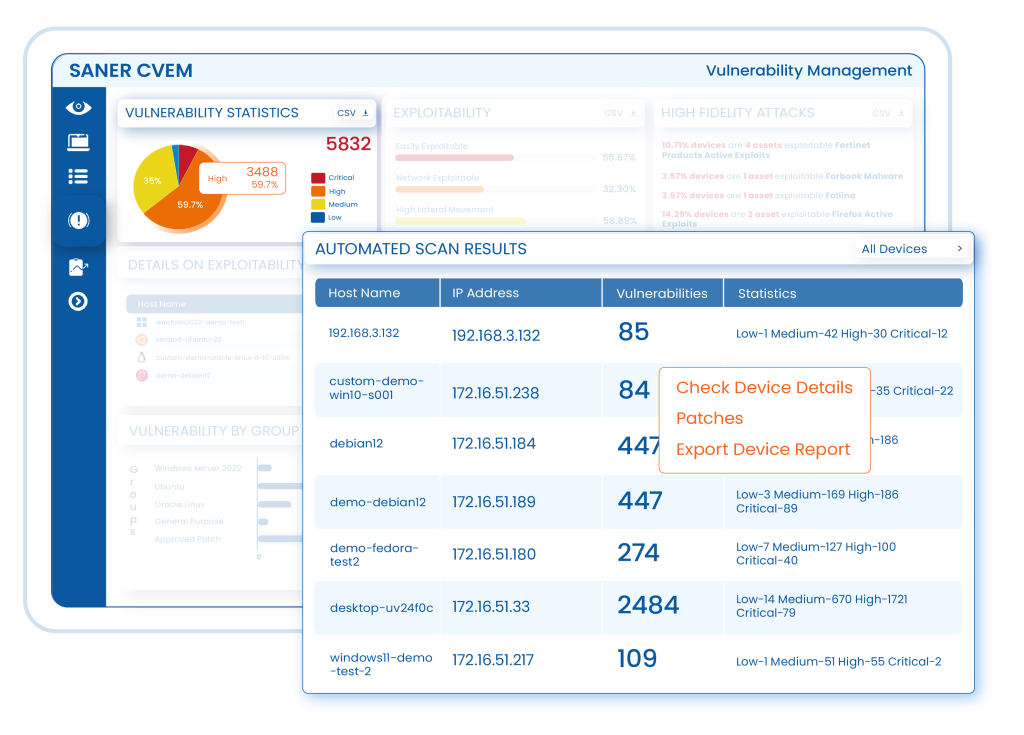
Prevent Asset Exploitation
Obtain an inventory of assets that are external facing and know which gain clarity on their exposures, including software vulnerabilities & misconfigurations.
Find Vulnerabilities from Every Nook and Corner
Detect vulnerabilities, misconfigurations & exposures from every technology asset with near-zero false positives.
Know the Greatest Threats
Reduce risk exposure at speed and scale, know which technology weaknesses pose the most threat and continuously monitor the attack surface.
Get Remediation Guidance
Reduce risk exposure at speed and scale, know which technology weaknesses pose the most threat and continuously monitor the attack surface.

Detect Security Gaps & Drive Compliance Risk Assessment Faster
Monitor Attack Surface 24x7
Monitor IT infrastructure from one platform & get clarity 24×7 with a complete overview of vulnerabilities & misconfigurations.
Verify Security Posture
Evaluate devices by monitoring more than 100 parameters through statistical analysis, ML and deviation computing to find hidden risks and implement cyber hygiene measures.
Prevent Targeted Attacks
Consolidate, contextualize and prioritize vulnerabilities to isolate high risk ones and minimize vulnerability backlog challenges to reduce attack surface.
Ease compliance Burden
Automate the compliance management process, create custom security policies, and address and fix configuration drifts to achieve cyber hygiene and get insightful compliance reports.
Solutions Crafted for Vulnerability Management
Understand how Saner Continuous Vulnerability & Exposure Management (CVEM) can effectively detect and remediate vulnerabilities and exposures and protect organizations from devastating cyberattacks.
HIGHLIGHTED CASE STUDY
Digital Banking Service Provider Achieves Instant Visibility of Risk Posture to Rapidly Remediate Risks, and Achieve Continuous Compliance
A Leading Digital Banking Service provider was looking for a vulnerability management solution to transform their IT security from a traditional security approach.
Get Exhaustive Visibility and Reduce Risk Exposure of your IT Infrastructure
Request a product walkthrough demo with one of our solution experts.

