Linux Vulnerability Management
Linux Vulnerability Management
Linux vulnerability management scans, detects, prioritizes, and remediates the flaws in the Linux environment. Every enterprise defines it in various ways. The unknown or known threats will exploit the flaws in the systems. It will aid in huge data loss and affects the whole enterprise without a vulnerability management tool. Now, let us know some weaknesses in Linux systems.
- Programming defects
- Weak configurations
Vulnerabilities in Linux got fancy names that were highly critical. They are as follows:
- GHOST
GHOST affected Glibc, and it is a common systems library.
- Heartbleed and POODLE
They mainly affected SSL/TLS that helped implement the network services.
- Shellshock
It showed up after the Bash flaw. They are used to attack devices and services. It is a highly critical vulnerability used in OpenSSL security protocol.
These fancy names represent flaws in the software systems, protocol designs, and lack of security checks in the program’s source code.
Vulnerability Scan in Linux
Like any other operating system, the Linux system also has flaws that lead to security vulnerabilities. A vulnerability scanning tool in Linux systems is a computer program that detects flaws in networks or applications. There are various Linux vulnerability scanning techniques. Vulnerability scans in Linux are important because hackers attack systems and networks on the internet constantly. So, daily scans will help secure your network and keep hackers at bay.
Now, let us understand how vulnerability management tool works in Linux systems.
How does it work in Linux systems?
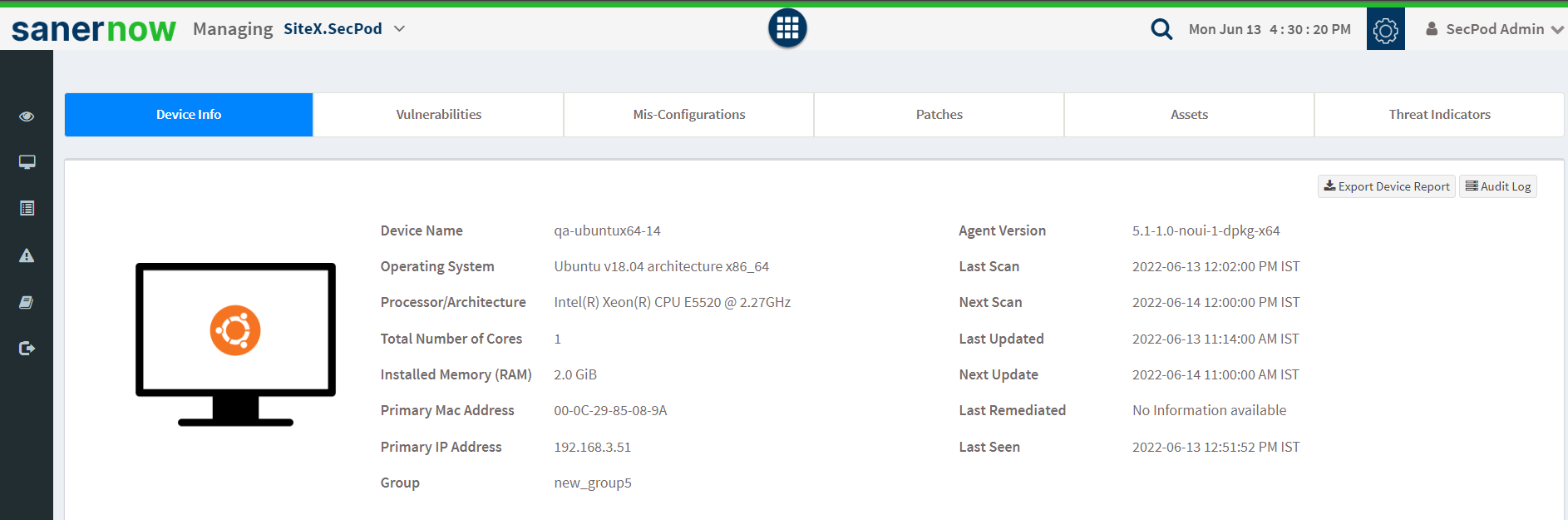
Let us walk through SecPod SanerNow Linux vulnerability management platform. You will gain clear insights into how Linux vulnerability scanning, assessment, and remediation will work in SanerNow. SecPod SanerNow supports major operating systems like Windows, Linux, and MAC. It is pretty easy and user-friendly to implement in all OSs.
SanerNow divides the whole vulnerability management system into six steps.
1. Rapid and automated Linux Vulnerability Scanning
SecPod SanerNow has an efficient vulnerability scanning algorithm that supports all major operating systems. With its intelligence-augmented, you can install a Saner agent supported to your system. Once installed, you can scan and detect flaws in less than five minutes on your devices. You can schedule scans and perform an ongoing vulnerability discovery as it is automated.
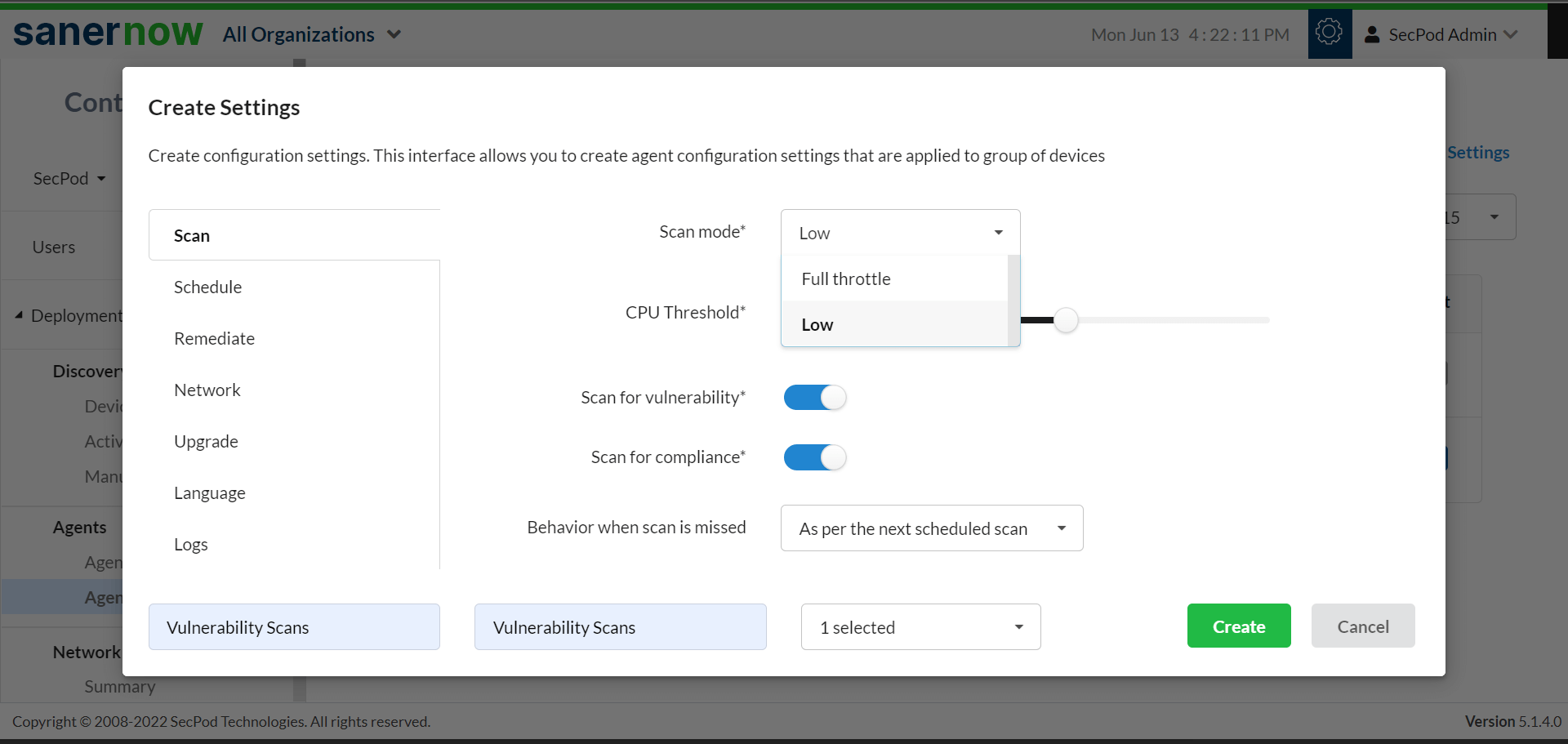
SecPod SanerNow also facilitates on-demand and real-time vulnerability scans in Linux. Also, it supports the world’s largest vulnerability database with precise detection.
2. Accurate detection of Linux vulnerabilities
Sanernow provides an effective vulnerability scan in the Linux system. SanerNow leverages the home-grown and world’s largest vulnerability database with 160,000+ security checks. Besides, the database will be updated regularly with the latest vulnerability information to ensure accurate detection. The lightweight agent is in constant sync with the database which detects vulnerabilities accurately with limited system resources and lesser bandwidth.
3. A thorough assessment of risks and potential exploits
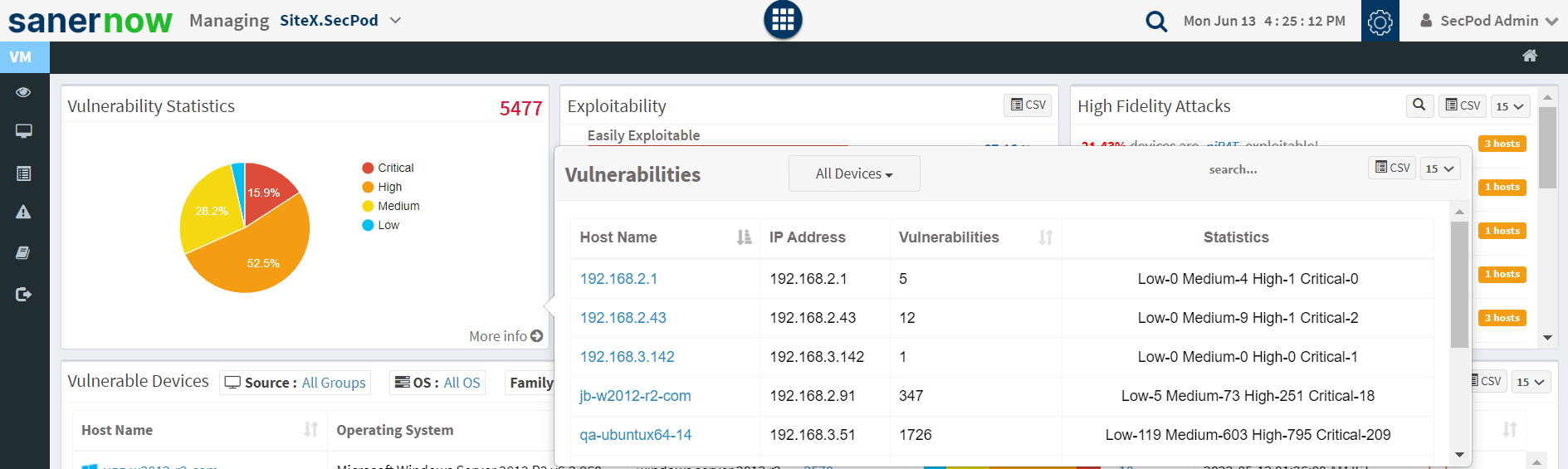
After successful Linux vulnerability scanning and detection of flaws, there will be a rigorous assessment based on the risk and severity level. Risk-based assessment will help in analyzing risk and its impact on the enterprise.
4. Predictive prioritization of risks based on the severity
Once the vulnerability scan in Linux machines is completed, all the data will be available in the SanerNow dashboard for further assessment. You can improve your Linux security posture by predicting the new exploits by historical details and their occurrence. However, CVSS scores will help to prioritize risk. We can combine risk-based and CVSS for effective vulnerability prioritization.
5. Integrated patching for faster remediation
Vulnerability remediation is one other task that many enterprises lag. Every enterprise uses various Linux vulnerability scanning techniques to detect flaws. However, they take a lot of time to remediate them. It results in security gaps and then leads to major exploits. SanerNow facilitates an integrated patch remediation module, that helps in quick remediation of flaws soon after detection.
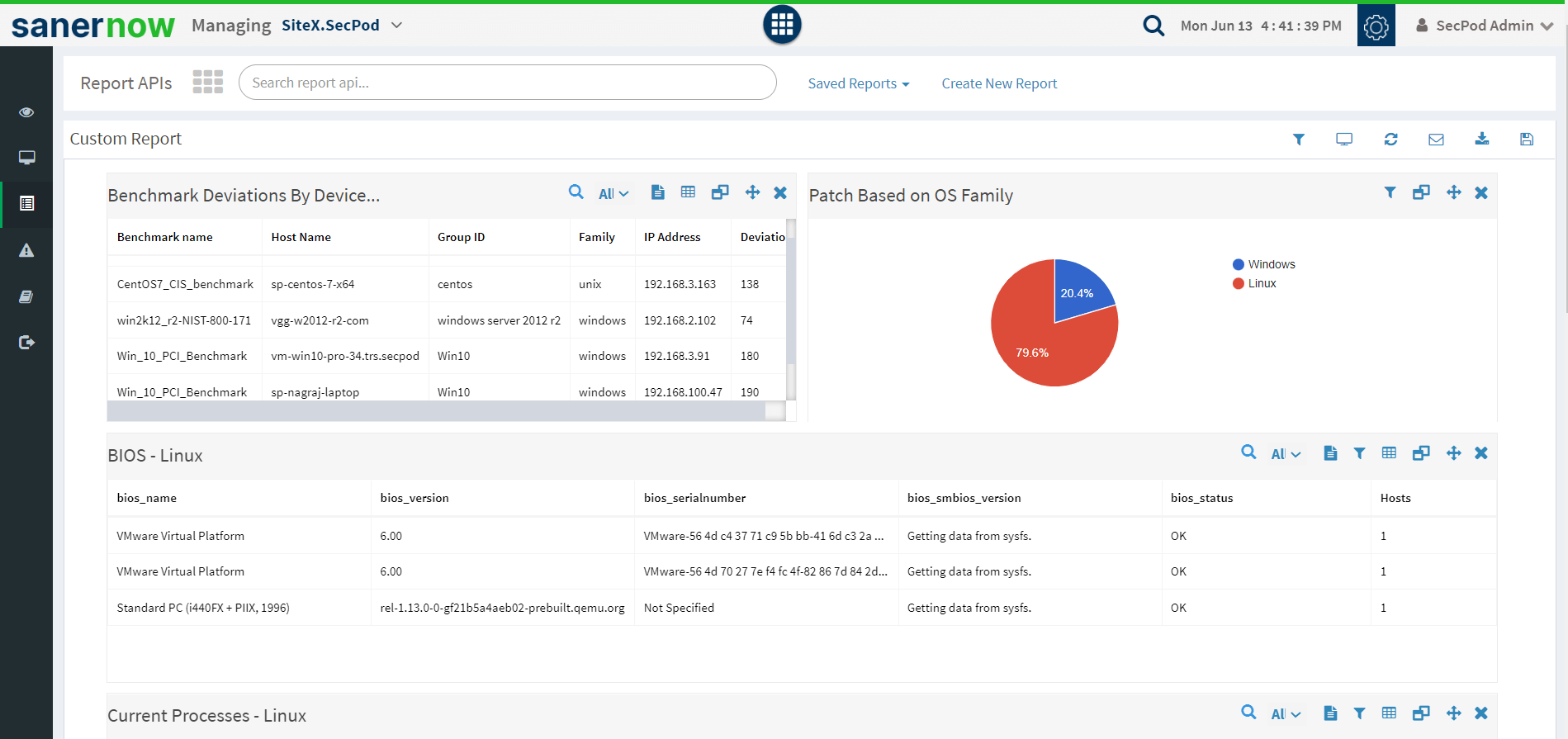
6. Customization of reports
With SanerNow you can customize comprehensive reports to analyze threats posing towards your enterprise. You will get actionable insights on flaws based on their type, device counts, exploitability, etc.
Supported versions in Linux systems
SecPod SanerNow supports various versions of Linux systems and provides real compatibility. SanerNow supports the following versions of Linux systems.
- Linux RPM: Red Hat Enterprise Linux 6.7, 7.3, 7.4, 7.5, 7.6, 8, Fedora 27, 28, 29, 30, 31, CentOS 6.x, 7.x, 8.x, Oracle Linux 6, 7, 8, Amazon Linux AMI, Amazon Linux 2
- Linux Debian: Ubuntu 14.04, 16.04, 18.04, 18.10, 19.04, 20.04, Debian 8, 9, 10, Linux Mint 17.x,18.x,19.x
- Linux Alpine: Alpine 3.6.x, 3.7.x, 3.8.x, 3.9.x, 3.10.x, 3.11.x
SanerNow provides total visibility and control over your endpoints and vulnerability remediation. It detects threats and remediates them instantly.
Supported servers in Linux systems
SecPod SanerNow is a security solution that works as a centralized cloud-based platform. It is a simple agent-sever-based model. The server has a simple user interface and supports both on-premises and cloud variants for enterprises to choose accordingly.

