Millions of people are robbed of personal data like their credentials, social security numbers, bank account-credit card details, among others, on social media. These can be stopped by using a vulnerability management tool. Cybercriminals are engaged in their thieving escapade to impersonate people on the internet. We usually see it on headlines that data theft led to breaches in privacy. Among these attacks, one that had a huge impact on the realm of cyber security was the 2017 cyberattack on Equifax. A Compliance Posture is necessary here.
The data breach had occurred in March 2017, and the threat actors had access to the database for 76 days. Sensitive information like Social Security Number, Driver’s License, etc. It had been accessed and was out in the interweb, ready to be abused. Automated patch management software can be of help here.
The fallout of this news was devastating as Equifax shares dropped by 13% the moment this news became public. But more importantly, Equifax had to pay over 1.4 billion dollars in settlement fees.
Equifax had been using the Apache Struts framework in systems that handled credit disputes. On March 7th, Apache released a critical patch that removed the vulnerability, which was the point of attack. Equifax decided that it wasn’t significant enough to patch and update their system. As a result, they became a perfect example of a company losing money, reputation, and credibility in the long list of non-compliant casualties.
Had Equifax followed stringent regulation policies, had they made compliance scanning a continuous process instead of an audit exercise. The story would have been entirely different.
What is Compliance? And What is Compliance Posture?
At its core, compliance means following rules and meeting standards set by regulatory bodies. This definition works for all domains, including cybersecurity. But a formal definition must be set.
“Cybersecurity Compliance encompasses following and meeting various controls, usually set by authoritative bodies. This is to maintain integrity, confidentiality, and protection of data.”
On the other hand, compliance posture provides visibility and control over IT assets and endpoints to strengthen and maintain compliance. It strives to achieve and sustain configuration standards while providing robust security to your IT assets.
Why is Cybersecurity Compliance Vital?
- Reduce Potential of Risks and Cyber-Attacks:
Rules are created for a reason, and compliance policies, in the case of cybersecurity, are designed to protect sensitive data and defend against cyber-attacks. Maintaining compliance reduces the attack surface, resulting in a safe and secure organization. - Increase Positive Reputation:
An obvious advantage of adherence to compliance policies is an increase in positive reputation. If an organization can keep its sensitive data safe and secure, it gains a positive reputation from the public, further enhancing the company’s public image. - Avoid Criminal Charges, Lawsuits, and Fines:
Hefty fines and criminal charges are usually the direct results of failing to maintain compliance with HIPAA(healthcare sector) violation fines ranging from USD 50,000 to USD 1.5 million a year. Similarly, other regulations like GDPR, PCI, etc., also charge and fine organizations on a case-by-case basis for breaking the compliance regulations. - Improve Business and Public Relation with Brand Compliance:
A company’s public image or brand dictates a lot of its business, and consequently, improving the brand helps in sales leading to success. While being compliant helps reduce risks, it also increases the public image, thus improving sales. The brand image becomes a virtue of the company and helps improve public relations.
Strengthening Compliance Posture Using SanerNow
With the number of cyberattacks rising every year, following strict regulations and taking additional steps to prevent cyber-attacks can make all the difference.
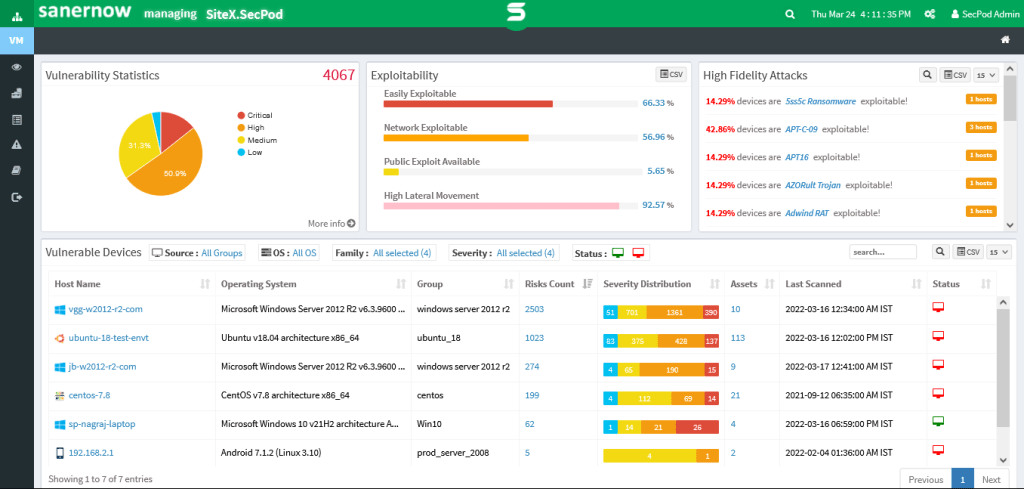
Using SanerNow, A continuous and advanced vulnerability management platform, achieving, enforcing, and maintaining compliance is as easy as clicking a button. With a wide array of tools to detect and remediate vulnerabilities, SanerNow provides 360-degree protection and prevention from cyberattacks.
However, SanerNow uses a revolutionary agent-server model. Moreover, a lightweight SanerAgent embeds the device, which works in cohesion with a repository or a server to collect, compare, understand and remediate vulnerabilities.
- Continuous and Real-Time Compliance Management with Customizable Policies:
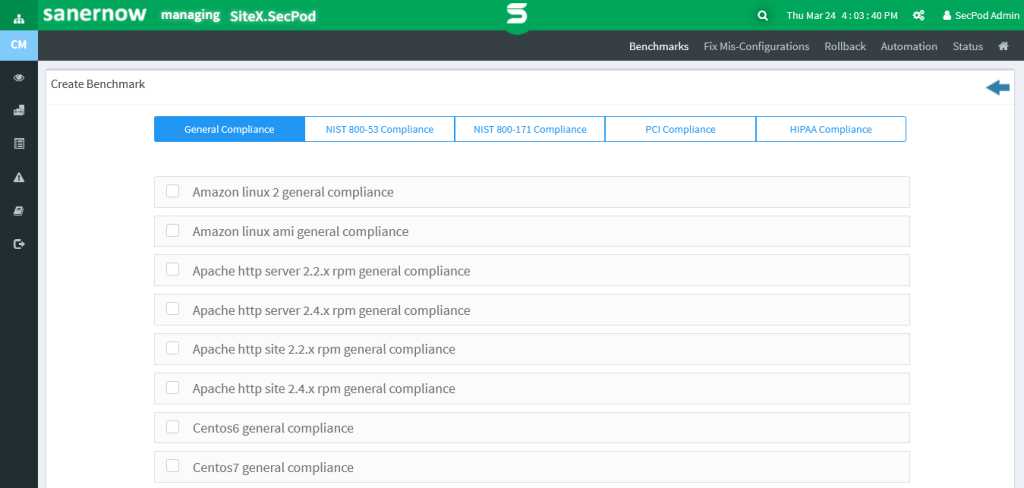
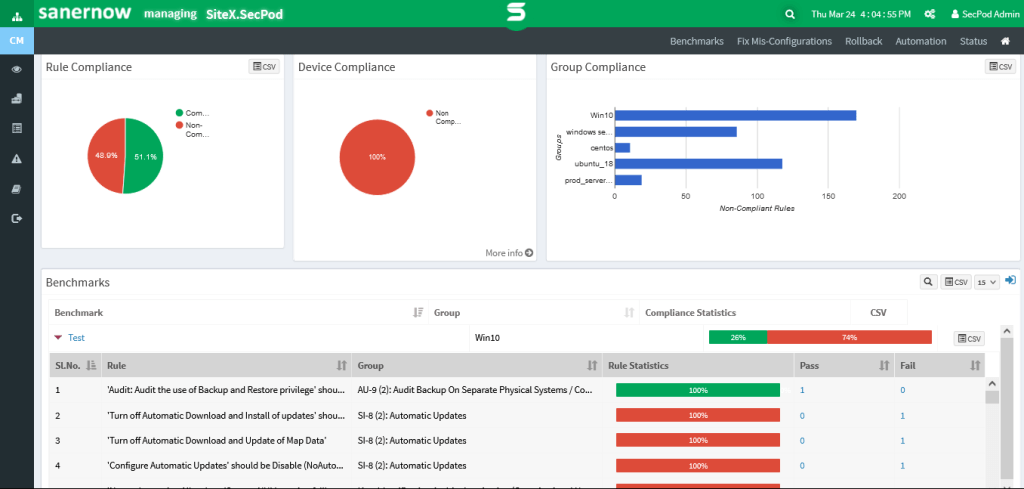
SanerNow helps enforce standard compliance policies like HIPAA, NIST, PCI, and more to a tee. It automatically detects new devices in the network, enforces compliance regulations on the said devices, and ensures their safety. SanerNow can also create custom compliance policies according to your needs to meet company standards. Along with the apparent benefit of safety and adherence to your domain’s compliance policies, your organization becomes invulnerable from lawsuits, charges, and fines.
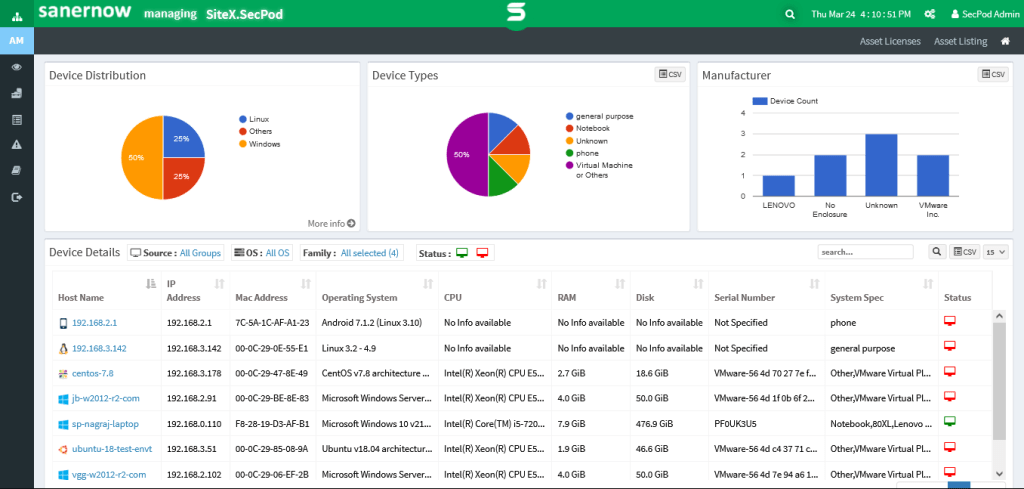
- Smart Asset Inventory and Exposure to Reduce Attack Surface :We can’t protect an endpoint if we do not know it exists or not. Discovering all assets becomes vital as vulnerabilities lurk in these endpoints, and remediating them takes center stage. SanerNow’s asset exposure tool works in the background tirelessly to detect and discover assets and provide complete visibility over your assets. With proactive system hardening in place, SanerNow minimizes the attack surface and helps prevent attacks, further improving the compliance posture of your organization.
Read More: Vulnerability Scanning Process
- Intelligent Risk and Vulnerability Management for Efficient Remediation: To improve compliance posture, eradicating vulnerabilities becomes vital, and a smarter assessment of risks and vulnerabilities makes this easier, faster, and cost-effective. Risk-based vulnerability management is the next step in intelligent vulnerability management. By analyzing various factors like threat context, CVE/CVSS score, exploitability etc. SanerNow prioritizes vulnerabilities intelligently. The prioritized vulnerabilities are quickly remediated by seamlessly integrating a patch management tool, further improving and strengthening compliance posture.
Read More: Risk-Based Vulnerability Management
Conclusion:
Compliance policies provide an excellent opportunity for organizations to strengthen and solidify their defense. Along with the benefit of safety and security, compliance offers a slew of other advantages while being cost-effective and cost-saving.
In addition, the consequence of not adhering to compliance policies can be devastating, and the effects long-lasting.
However, with SecPod’s SanerNow, compliance management is as easy as it can get. Moreover, with a plethora of features, from continuous compliance and scanning to customizable policies, SanerNow helps you achieve, maintain and bolster your defense.
We are SecPod and we prevent cyber-attacks.
Schedule a free demo now!!