Anti-virus is dead?
Anti-virus or Anti-malware is not dead; it is one of the defense mechanism in a defense-in-depth strategy. Here is the…
Anti-virus or Anti-malware is not dead; it is one of the defense mechanism in a defense-in-depth strategy. Here is the…
A bit of a background on buffer overflow to begin with. A buffer overflow occurs when a program tries to…
what is a buffer? In general, the term buffer is a temporary storage, a space in the memory used to…
A new kind of botnet in cyber security has been uncovered which takes an innovative approach to find security vulnerabilities…
It took us close to nine months to translate our idea into reality. We had debated the idea (for ANCOR,…
IDA Pro is primarily a multi-platform, multi-processor disassembler that translates machine executable code into assembly language source code for the…
Steganography is an art of hiding a message, image, or file within another message, image, or file.
Most images are used to hide the data. The flexibility of using images means that information can be hidden in a variety of ways. It can be scattered all over the image or inserted straight inside.
If data is inserted straight inside. we can find it easily using the below technique,
Hex Editor
like HexEdit, HxD on windows
using :%!xxd command on Linux
FF D8
FF D9
EOI (End Of Image) marker

Here is an example to insert data straight inside the image without any tool on windows:
copy /b original.jpg + "hidden data.txt" "hidden image.jpg"
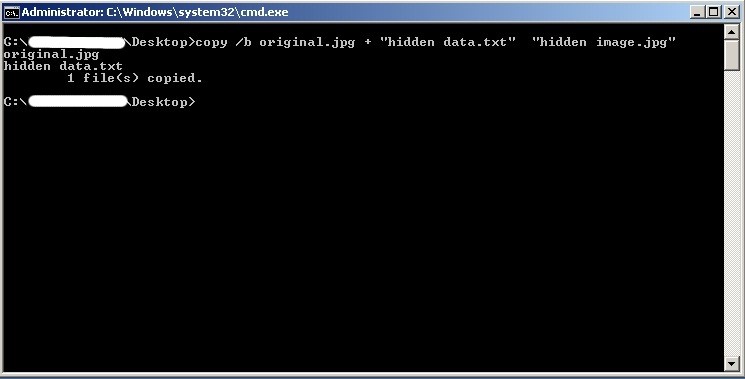
A new image will be created with your data hidden. You can open and view that image normally.
But, to view the hidden content open that image in any Hex editor as mentioned above and see the hidden data at the end after the EOI marker.
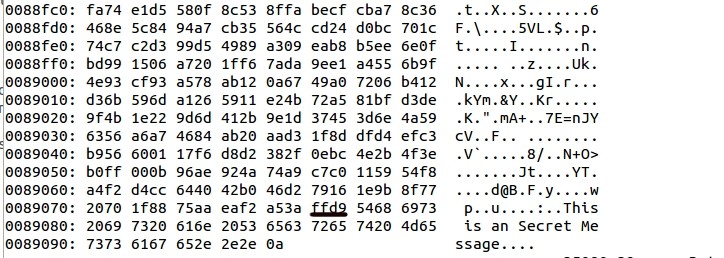
Later, a quick obfuscation layer is added (Password or key) to hide the visibility of the data in the HEX format. To view the original message we need that key or password.
Here is an example to insert data inside the image using Outguess tool:
outguess is one of the tool that allows the insertion of hidden information into
the redundant bits of data sources.
Data Hiding :
outguess -k "secretkey" -d hidden.txt image.jpg out.jpg
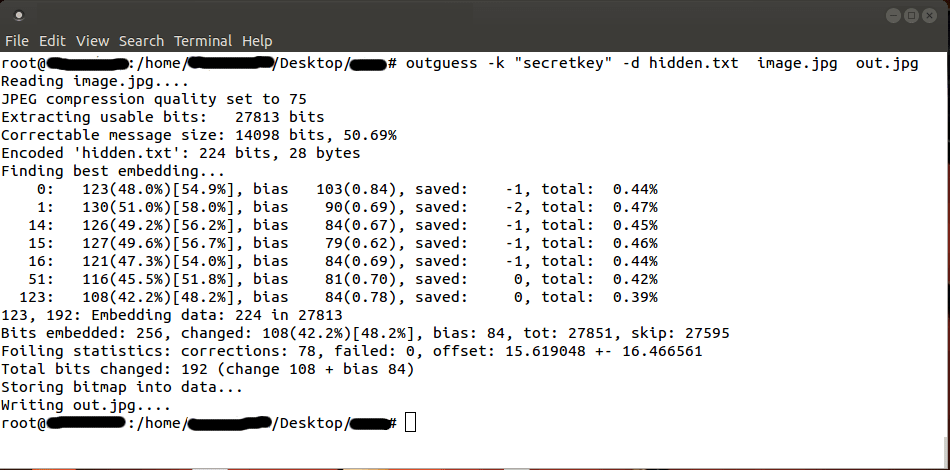
(more…)Data Retrieval :
outguess -k "secretkey" -r out.jpg hidden.txt
There are times when we need to run some Windows applications (.exe, .msi) on Linux. This objective can be achieved…
One of the most common memory corruption errors usually found in an application is the “Double Free” error. Double-free vulnerability…
Any program intended to disrupt computer or network operation, gather sensitive information, or gain access to private computer systems or…