A new kind of botnet in cyber security has been uncovered which takes an innovative approach to find security vulnerabilities in the website using systems installed with illegitimate Mozilla Firefox add-on. An investigation by KrebsOnSecurity has revealed. Using a vulnerability management solution.
The “Advanced Power” botnet in cyber security has already infected more than 12,500 systems. It
installs itself as a legitimate Mozilla Firefox add-on/extension and helped cyber-criminals to identify SQL injection vulnerabilities in 1,800 websites. This is why it is important to have a patch management solution.
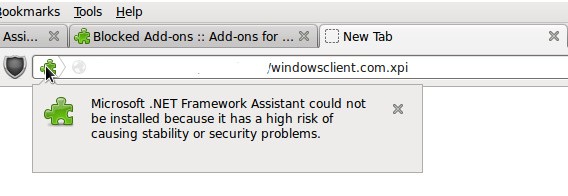
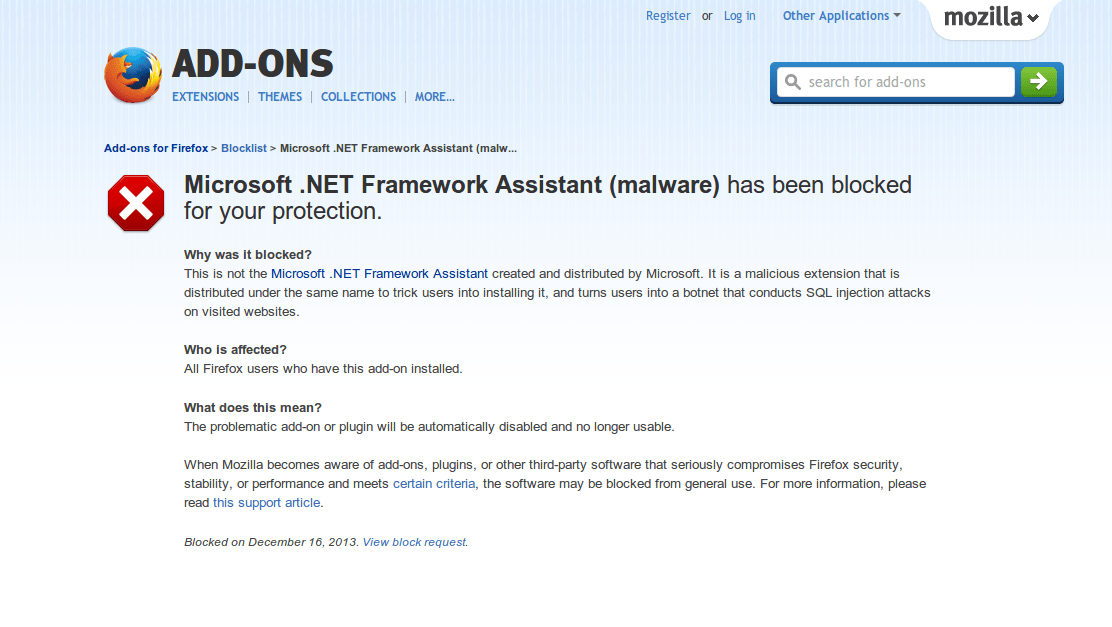
Once malware gets into the system, it installs a Mozilla Firefox bogus “Microsoft .NET Framework Assistant” add-on. It is a malicious add-on that has the same name as of legitimate add-on tricking users to install. The malicious add-on then searches for all the pages visited by the victim for SQL injection vulnerabilities.
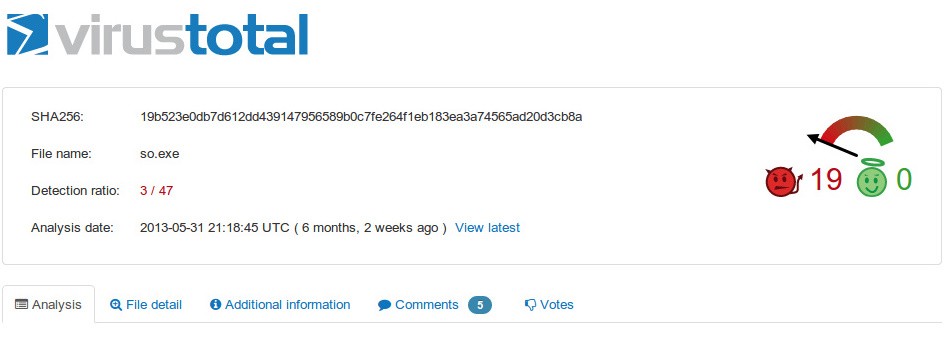
The botnet has been first spotted in 31st May 2013 according to malware analysis service Malwr
SHA256 19b523e0db7d612dd439147956589b0c7fe264f1eb183ea3a74565ad20d3cb8a
and at that time only 3 antivirus applications out of 47 (as shown in below picture) were able to identify this as malicious code according to Virus Total, which is very low detection rate.
Advanced Power malware has been distributed at least in part by the Blackhole exploit kit according to “Kafeine” @ Malware Don’t Need Coffee blog.
Also, Mozilla has blocked bogus “Microsoft .NET Framework Assistant (malware)” add-on used by the Advanced Power botnet.
Attackers are using very deep and innovative approaches to bypass various defensive techniques. However, Antivirus alone is not enough to protect against these attacks. Also, install applications/add-ons only from authors whom you trust and keep your browsers up-to-date to avoid attacks. Download Saner and keep your systems updated and secure.
– Veerendra GG