A team of cybersecurity researchers found multiple vulnerabilities that affect billions of devices that run on either Windows or Linux. Affected devices include laptops, servers, workstations, or even IoT devices. Boot hole vulnerabilities affect Linux and other Operating Systems using GRUB@ boot loader where secure boot truest the 3rd-party UEFI CA. If and when this is exploited, the Operating system’s booting process can be compromised to execute arbitrary code. These vulnerabilities can be mitigated using patch management tool.
What are a Bootloader and UEFI?
A bootloader acts as a bridge between the hardware and operating system. It works by loading the working memory of the OS first and then the OS’s Kernel in the respective order. Attackers can take over the system’s boot process and execute malicious code. It was also discovered that even when the Secure boot option was turned on by the OS, the attackers can still exploit it, thus rendering the Secure-Boot feature impractical. To be more secure and safe, vulnerability management tool is a great solution.
Unified Extensible Firmware Interface (UEFI) stands for, and it actively prevents the loading of operating system components and firmware drivers that do not possess a trusted signature. UEFI thus defends the boot process against untrusted code execution.
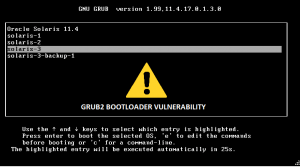
GRUB2 Vulnerabilities:
Multiple Vulnerabilities are assigned for this exploit, one of them being CVE-2020-10713 that exploits the GRUB2 cfg verification process.
CVE-2020-10713
This vulnerability termed “Hole in the Boot” or boothole vulnerability allows an attacker to load a malicious kernel instead. Once the attacker has physical or remote access to the system within the same network, they can craft a string as a malicious payload that causes a buffer overflow, leading to the execution of arbitrary code.
Grub configuration file “grub.cfg” is a primary attack vector of this vulnerability, and this text file lacks the integrity verification method. Thus any modification implicated over the file can reflect changes in the Operating System’s booting process. Also, the alteration made is persistent, which means even changing OS does not remove the malicious or misconfigured cfg file.
CVE-2020-14308
This vulnerability affects the GRUB2 version before 2.06. The grub memory allocator does not check for arithmetic overflows on the requested allocation size. In turn, the function generates invalid memory allocations, which attackers can exploit to potentially cause integrity, confidentiality, and availability attacks during the booting process.
CVE-2020-14309, CVE-2020-14310
Attack vectors for CVE-2020-14309 is grub_squash_read_symlink and for CVE-2020-14310 is read_section_from_string according to Ubuntu advisory. In these vulnerabilities, GRUB2 cannot handle certain filesystems like font files, which leads to multiple integer and heap-based buffer overflow. An attacker with local access can then use these to bypass UEFI secure-boot and cause arbitrary code execution.
CVE-2020-14311
In this vulnerability, GRUB2 cannot handle specific filesystems, font files, or PNG images, which leads to multiple integer and heap-based buffer overflow. An attacker with local access can then use these to bypass UEFI secure-boot and cause arbitrary code execution.
More GRUB2 Vulnerabilities:
CVE-2020-15705
This CVE affects GRUB2 with version 2.04 and prior. This vulnerability allows bypassing secure boot with a malicious kernel because GRUB2 fails to validate the kernel signature. However, it only affects cases where the kernel signing certificate is imported directly without using a shim package. Shim is an EFI application.
CVE-2020-15706
This vulnerability also affects GRUB2 version 2.04 and prior. Its affected by a race condition in grub_script_function_create() component leading to a use-after-free vulnerability. This vulnerability is triggered when a function is reinitialized, and the same function was already being executed, which leads to arbitrary code execution and secure boot bypass.
CVE-2020-15707
This vulnerability affects GRUB2 version 2.04 and earlier. Function grub_cmd_initrd and grub_initrd_init in the efilinux component of GRUB2. Heap-based buffer overflow can trigger by many arguments to the initrd command on 32-bit architectures or a crafted filesystem with huge files on any architecture. Thus leading to arbitrary code execution and secure boot bypass.
Affected products and OS
GRUB2 version 2.06 and prior.
Linux systems
Windows 8.1, 10, Server 2012, Server 2016, Server 2019
Impact
Attackers can exploit these critical vulnerabilities to execute arbitrary code and bypass Secure Boot restrictions.
Solutions to boothole vulnerability
Linux vendors have advised patching affected packages. In the case of Windows, Microsoft has released an untested dbx update for users who urgently patch the issue. Microsoft stated that “they are working on completing validation and compatibility testing of a required Windows Update that addresses this vulnerability.”
SanerNow detects this vulnerability and automatically fixes it by applying security updates for Linux systems. Download SanerNow and keep your systems updated and secure.