In today’s world, organizations constantly face cyber threats and vulnerabilities that can compromise their sensitive data, disrupt operations, and damage their reputations. The biggest challenge for IT Security Teams is to handle the mountainous volumes of vulnerabilities being detected by vulnerability scanners. Hence, prioritizing vulnerabilities must be a crucial part of any organization’s cybersecurity strategy. Having a vulnerability management tool is not enough without knowing which critical vulnerabilities to address first. More and more IT Security teams are realizing this and prioritizing their vulnerability remediation activities.
Institutions such as CISA have been creating a huge impact here for IT Security folks by introducing vulnerability prioritization frameworks such as SSVC, EPSS, and more.
Once you prioritize which vulnerabilities to act upon first, you can easily patch them using a patch management tool. This makes it easier for your organization to save time by patching the critical ones rather than patching every discovered vulnerability. Here are five reasons why organizations prioritize vulnerabilities.
1. Effective Risk Management:
Not every organization has an army of Security specialists. Prioritizing vulnerabilities allows organizations to focus their resources on the most critical security issues first. By prioritizing vulnerabilities based on the severity level, business impact, and potential impact of an exposure being exploited, organizations can manage risks more effectively. Also, narrowing down the vulnerabilities to remediate immediately saves the organizations tons of time and human effort. This way, each organization can focus on the most critical vulnerabilities and take action to remediate them rather than patching every vulnerability.
2. Compliance:
Regulatory standards, such as ISO, HIPPA, and PCI, require organizations to prioritize vulnerabilities and remediate them in a timely manner. Actively prioritizing vulnerabilities and effectively remediating them helps organizations meet their compliance requirements. Giving importance to compliance can help you become a trustworthy business. Avoid facing hefty fines or facing potential lawsuits due to negligence. Maintain a clear standard of what you can and cannot do and how your business should operate. Make employees feel that they work in a secure and professional environment.
3. Efficient Use of Resources:
Prioritizing vulnerabilities help organizations allocate their resources more efficiently. By focusing on the most critical vulnerabilities first, organizations can avoid wasting resources addressing low-risk vulnerabilities while higher-risk vulnerabilities remain unaddressed. Such organized processes keep team members motivated and engaged.
4. Building Trust with Customers and Partners:
Continuously prioritizing vulnerabilities and taking effective actions to remediate them successfully builds trust in the company’s values. Customers and Partners will trust the company and make decisions that will benefit the company in numerous ways. It brings a sense of belief that the organization takes a proactive approach to cyber security.
5. Continuous Improvement:
Prioritizing vulnerabilities is an ongoing process that allows organizations to improve their security posture continuously. By regularly assessing vulnerabilities and prioritizing them based on their risk level, organizations can stay ahead of potential threats and reduce the risk of cyberattacks and data breaches.
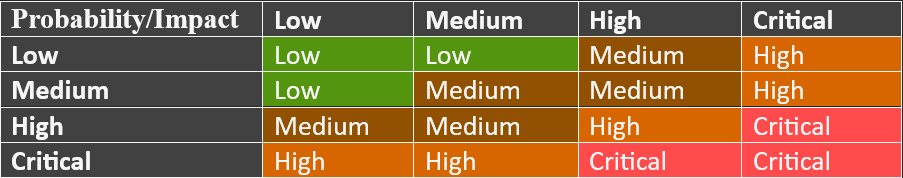
To prioritize vulnerabilities, organizations use several methods, including severity-based prioritization, exploitability-based prioritization, exposure-based prioritization, business context-based prioritization, and threat intelligence-based prioritization. By combining these, organizations can achieve a more comprehensive and accurate understanding of the risk landscape and prioritize vulnerabilities more effectively. This helps them to allocate resources more efficiently and maintain a strong security posture.
Vulnerability Prioritization Matrix
Conclusion
Organizations prioritize vulnerabilities to manage risks more effectively, meet compliance requirements, allocate resources more efficiently, build trust with remediation owners and service owners, and continuously improve their security posture. By following this, organizations can stay ahead of potential threats and reduce the risk of cyberattacks and data breaches.