Ransomware has made its way into the consciousness of business owners and security admins over the past two years. As an increasingly prevalent cyberattack, ransomware has grabbed more headlines than any other cyberattack in 2021. According to a recent study by Cybersecurity Ventures, in every 11 seconds ransomware attacks have been halting businesses. With close to 714 million ransomware attacks by the end of 2021, things are only going to get worse in the following year if a good vulnerability management software is not utilized.
Statistics and Impact of Ransomware Attacks in 2021
Never in the faintest dreams, security admins and cybersecurity experts thought that 2021 would be a year of the cyber surge. In addition, hackers can wreak havoc with an 11-second window into an organization’s digital infrastructure. Even the much-awaited winter holiday season was disrupted with the inception of the Log4j vulnerability.
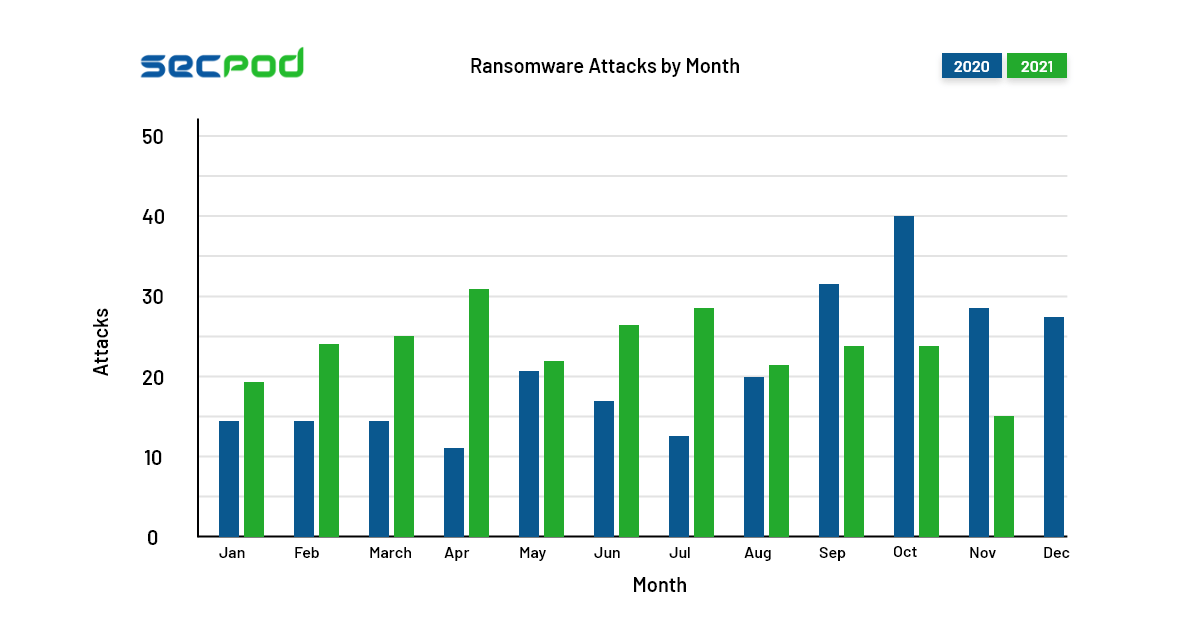
Ransomware attacks have transcended into a business model. With the birth of RaaS, Ransomware-as-a-Service, anyone can get into a business and install malware. It often becomes hard to track the attacks as ransom is paid by a peer-to-peer exchange of digital currency or, simply put, cryptocurrency. In January 2021 alone, 19 ransomware attacks were recorded globally. The attacks were ranged across different business verticals like Apex Lab, a Phlebotomy giant, to DSC Logistics, a notable third-party supply chain management based out of Illinois. Prevent such attacks from patching your devices regularly with a good patch management software.
The ransomware attacks in 2021 Q1 were three times in number compared to attacks in 2019. The attackers generally hold businesses for ransom that ranges from $30,000 to $250,000. This year, the damage rendered by ransomware attacks was 57x times more significant than in 2015, i.e., a total of $20 billion(and counting).
Ransomware gangs like HelloKitty, Mount Locker, PYSA, Darkside, Conti, Clop, REvil, Egregor, among hundreds of others, became common names to the ears of security admins. Ransomware is currently the fastest cybercrime which grows exponentially compared to its counterparts.
Extortion leads to Ransomware Attacks
Ransomware is nothing without the extortion part. Black hat hackers are notorious, some do it for the kicks or impulses, and some do it to make money. Today with inflation on the rise, almost all bad actors are getting into the bandwagon of making huge bucks through extortion, better yet, exploitation.
With the internet and limitless digitalization, the world has become an oyster. With a few clicks, you can get food delivered to your doorstep. And there is the dark side, where criminals can take down an organization and get its security team to its knees with a few clicks. Even the best security teams cannot protect themselves from ransomware if there is a small loophole in IT infrastructure.
Extortionists behind the criminal organizations threaten top companies to leak sensitive information of their customers/clients to the outside world. The scenario can dissolve the company into mist in a day’s time. In 2022, the practice of extortion is only going to worsen. This calls forward the need for upgrading defenses. With the arrival and massive use of Ransomware 3.0 or Nuclear Ransomware 3.0, cybercriminals won’t just encrypt files, instead leak the information. The aftermath of the information being public could jeopardize the image of the company, affects its stock price as well as its profits.
Holding on to the conventional approach won’t protect you for a long time. Stopping sophisticated ransomware attacks needs a multi-faceted approach and understanding the importance of cyber health. For instance, security teams need to rely on tools that provide transparency to exposures — robust methods to detect unprecedented attacks.
Ransomware Attacks won’t be slowing down in 2022
As 2021 is almost about to end, with a new year in the making, new challenges in safeguarding and protecting devices await us. Ransomware will become much more aggressive in the coming year. Businesses need to bring in new tactics to fend off a rampant rise in ransomware attacks. The use of RaaS will continue to grow as the affiliate model makes it easier for anyone to launch cyberattacks.
With RaaS, attackers can extort double the ransom, which is already a threat that cybersecurity experts have experienced. As RaaS cartels and syndicates are growing in number, a person without any technical skillset can launch their cybercrime operations and run them remotely.
Then there is a remote access ransomware model, which in a cybercriminal ecosystem is regarded as Access-as-a-Service. With this model, people can sell and exchange credentials, which further compromises any website or even service. The combined prowess of these bleeding-edge cybercriminal technologies can bring a new frontier into ransomware attacks. Anyone with a despicable mindset could pay to cybercrime syndicates, leverage them, and successfully deploy ransomware.
Major Ransomware Trends to look out for in 2022
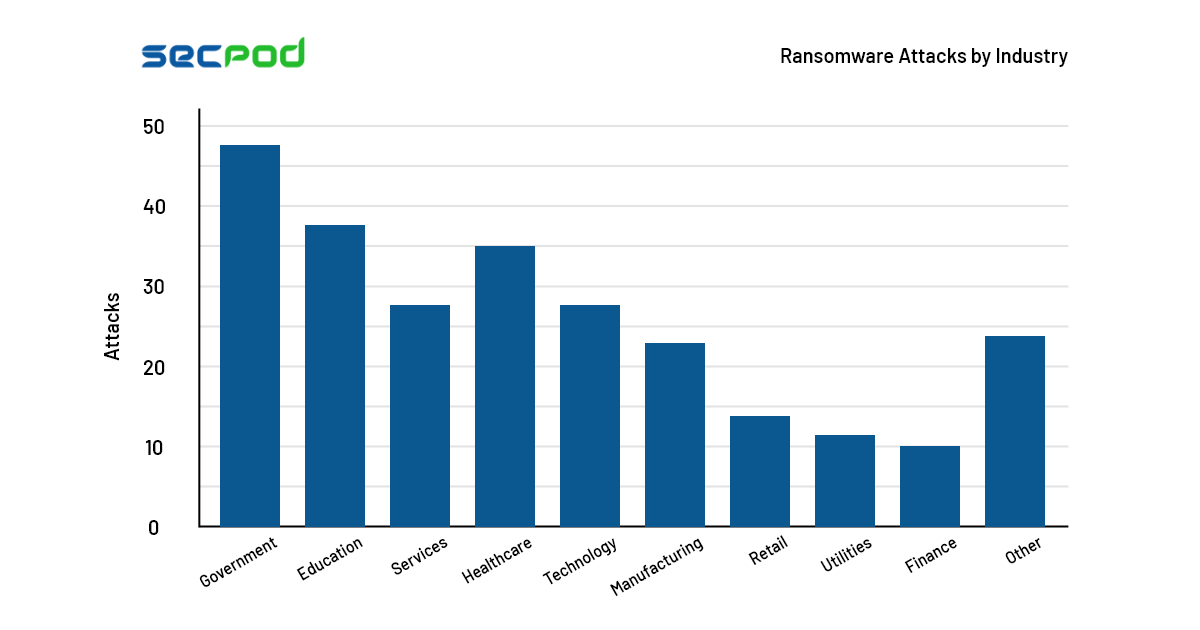
Cybercriminals are often drawn to supply chains. The massive is the customer base; the devastating will be the attacks. As compared to the yesteryears, supply chain attacks increased by fourth-fold in 2021. Moreover, around 42% of the healthcare and medical centers were also inflicted by ransomware attacks. Further, compromising patient records, staff records, medical equipment, among others. Then there are businesses from other verticals that greatly benefitted from digital transformation. Work from home has been a blessing in disguise for employees but a curse for security teams and cybersecurity experts.
For any ransomware or any other cyberattack, the absence of visibility plays a crucial role. The Kaseya ISV breach will be remembered till the end of time. With this attack, cybersecurity experts aren’t the only ones to have procured information. Given that the attack was a wake-up call for industry as a whole, the blueprint of the attack is already out. Even the bad actors know how they can take down Fort Know without breaking a sweat.
Let’s explore four significant trends that cybercriminals will follow in 2022 to launch successful attacks:
- Ransomware syndicates might put the lives of innocents in jeopardy by engaging in “pile-on.”
- Supply chains practice commoditization. An increase in supply and demand would bring successful ventures into the crosshair of attackers.
- The use of firmware malware could make it easier for attackers to breach any digital infrastructure.
- The hybrid workforce will continue to be a prevailing reason for allowing attackers to take control of devices.
All businesses can do is brace themselves for an unprecedented increase in cyberattacks and curate strategies by relying on cybersecurity tools that will strong-arm them.
Be Cyber-ready with SanerNow
Fear has been the greatest motivator to protect computer systems and networks from bad actors. However, today something as simple as fear isn’t enough to protect your digital assets. Continuous vulnerability scanning and timely remediation are required to orchestrate a proper CyberHygiene routine.
SecPod SanerNow Vulnerability Management provides comprehensive visibility over vulnerabilities in the network by scanning all the devices. With an industry-leading scanning time of fewer than 5 minutes, SanerNow offers the fastest vulnerability scans. SanerNow leverages the world’s largest vulnerability management database with over 160,000 security checks to detect vulnerabilities accurately. It also assesses and prioritizes the vulnerabilities based on the severity range. The integrated patch management in SanerNow enables faster remediation on all operating systems and 300+ third-party applications.
Along with Vulnerability Management, you can also leverage the top cyber hygiene features from other SanerNow applications like IT asset Management, Endpoint Management, and Compliance Management.
Schedule a demo here to watch SanerNow in action and be cyber-ready anytime and anywhere.
Source: Cybersecurity Ventures