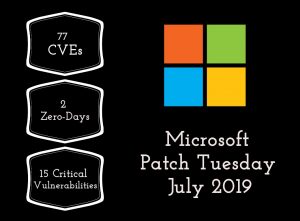
Microsoft Patch Tuesday July 2019 released its monthly set of security updates today. 77 vulnerabilities were addressed in these updates with 15 vulnerabilities rated critical and 62 vulnerabilities rated important in severity all done using a vulnerability management tool. All the critical vulnerabilities lead to remote code execution. 51 vulnerabilities were addressed in Windows alone.
Microsoft also fixed an elevation of privilege vulnerability (CVE-2019-1130) in Windows disclosed by SandboxEscaper aka Polar Bear. This is a flaw in the Windows AppX Deployment Service (AppXSVC) due to improper handling of hard links. An attacker who is logged in can take control of the system by running specially crafted applications. A patch management solution can stop these attacks.
One of the critical vulnerabilities that needs attention is CVE-2019-0785. A memory corruption flaw in the Windows DHCP Server allows an unauthenticated attacker to run arbitrary code on DHCP failover server. This vulnerability affects Windows Server 2012, Windows Server 2012 R2, Windows Server 2016 and Windows Server 2019.
System administrators are advised to keep their machines up-to-date by installing all the latest patches. Please install the updates issued for zero-days and critical vulnerabilities at the earliest as active exploitation has been reported.
Privilege escalation zero days
Microsoft issued updates for two privilege escalation zero-days this month. CVE-2019-1132 is considered particularly important as there have been reports of in-the-wild exploitation of this vulnerability by the Russian state-funded hackers. But an attacker needs to be logged in to the system to exploit these vulnerabilities.
CVE-2019-1132 is a vulnerability in Win32k component of Windows. Successful exploitation allows an attacker to run arbitrary code in kernel mode and take control of a system. The systems affected by this vulnerability are Windows 7, Windows Server 2008 and Windows Server 2008 R2.
CVE-2019-0880 is a local elevation of privilege vulnerability in the handling of calls by splwow64. Successful exploitation allows an attacker to elevate privileges from low-integrity to medium-integrity. Windows 10, Windows 8.1, Windows Server 2012, Windows Server 2012 R2, Windows Server 2016 and Windows Server 2019 are affected by this vulnerability.
Publicly disclosed Vulnerabilities
Six publicly disclosed vulnerabilities were addressed in these updates.
- CVE-2019-0865 – An important denial of service vulnerability in SymCrypt due to improper handling of digital signatures.
- CVE-2018-15664 – An elevation of privilege vulnerability in Docker runtime due to improper handling of symbolic links. Microsoft advises Azure Kubernetes Service (AKS) and Azure IoT Edge customers abstain from the use of the Docker copy command on their AKS clusters and Azure IoT Edge devices.
- CVE-2019-0962 – An elevation of privilege vulnerability in Azure Automation which allows members of an organization to access the Key Vault secrets through a runbook.
- CVE-2019-1068 – A remote code execution vulnerability in Microsoft SQL Server due to incorrect handling of the processing of internal functions.
- CVE-2019-1129 – An elevation of privilege vulnerability in Windows AppX Deployment Service due to improper handling of hard links. An attacker can take complete control of the system by running specially crafted code.
- CVE-2019-0887 – A remote code execution vulnerability in Remote Desktop Services (or Terminal Services) which allows an authenticated attacker to execute arbitrary code on the affected system.
July 2019 Patch Tuesday release consists of security updates for the following products:
- Microsoft Windows
- Internet Explorer
- Microsoft Edge
- Microsoft Office and Microsoft Office Services and Web Apps
- Azure DevOps
- Open Source Software
- .NET Framework
- Azure
- SQL Server
- ASP.NET
- Visual Studio
- Microsoft Exchange Server
Microsoft security bulletin summary for July 2019:
- Product : Microsoft Windows
CVEs/Advisory : ADV190020, CVE-2019-0785, CVE-2019-0811, CVE-2019-0865, CVE-2019-0880, CVE-2019-0887, CVE-2019-0962, CVE-2019-0966, CVE-2019-0975, CVE-2019-0999, CVE-2019-1006, CVE-2019-1037, CVE-2019-1067, CVE-2019-1071, CVE-2019-1073, CVE-2019-1074, CVE-2019-1082, CVE-2019-1084, CVE-2019-1085, CVE-2019-1086, CVE-2019-1087, CVE-2019-1088, CVE-2019-1089, CVE-2019-1090, CVE-2019-1091, CVE-2019-1093, CVE-2019-1094, CVE-2019-1095, CVE-2019-1096, CVE-2019-1097, CVE-2019-1098, CVE-2019-1099, CVE-2019-1100, CVE-2019-1101, CVE-2019-1102, CVE-2019-1108, CVE-2019-1116, CVE-2019-1117, CVE-2019-1118, CVE-2019-1119, CVE-2019-1120, CVE-2019-1121, CVE-2019-1122, CVE-2019-1123, CVE-2019-1124, CVE-2019-1126, CVE-2019-1127, CVE-2019-1128, CVE-2019-1129, CVE-2019-1130, CVE-2019-1132
Impact : Denial of Service, Elevation of Privilege, Information Disclosure, Remote Code Execution, Security Feature Bypass
Severity : Critical
KBs : 4507435, 4507448, 4507449, 4507450, 4507452, 4507453, 4507455, 4507456, 4507457, 4507458, 4507460, 4507461, 4507462, 4507464, 4507469
2. Product : Internet Explorer
CVEs/Advisory : CVE-2019-1001, CVE-2019-1004, CVE-2019-1056, CVE-2019-1059, CVE-2019-1063, CVE-2019-1104
Impact : Remote Code Execution
Severity : Critical
KBs : 4507434, 4507435, 4507448, 4507449, 4507450, 4507452, 4507453, 4507455, 4507458, 4507460, 4507462, 4507469
3. Product : Microsoft Edge
CVEs/Advisory : CVE-2019-1001, CVE-2019-1062, CVE-2019-1092, CVE-2019-1103, CVE-2019-1104, CVE-2019-1106, CVE-2019-1107
Impact : Remote Code Execution
Severity : Critical
KBs : 4507435, 4507450, 4507453, 4507455, 4507458, 4507460, 4507469
4. Product : Microsoft Office and Microsoft Office Services and Web Apps
CVEs/Advisory : CVE-2019-1006, CVE-2019-1084, CVE-2019-1105, CVE-2019-1109, CVE-2019-1110, CVE-2019-1111, CVE-2019-1112, CVE-2019-1134
Impact : Elevation of Privilege, Information Disclosure, Remote Code Execution, Spoofing
Severity : Important
KBs : 4018375, 4461539, 4462224, 4464534, 4464543, 4464558, 4464565, 4464572, 4464592, 4475509, 4475510, 4475513, 4475514, 4475517, 4475519, 4475520, 4475522, 4475527, 4475529, 4475545
Some more Microsoft security bulletin summary for July 2019
5. Product : Azure DevOps
CVEs/Advisory : CVE-2019-1072, CVE-2019-1076
Impact : Remote Code Execution, Spoofing
Severity : Critical
6. Product : .NET Framework
CVEs/Advisory : CVE-2019-1006, CVE-2019-1083, CVE-2019-1113
Impact : Denial of Service, Elevation of Privilege, Remote Code Execution
Severity : Critical
KBs : 4506986, 4506987, 4506988, 4506989, 4506991, 4507411, 4507412, 4507413, 4507414, 4507419, 4507420, 4507421, 4507422, 4507423, 4507435, 4507450, 4507455, 4507458, 4507460
7. Product : SQL Server
CVEs/Advisory : CVE-2019-1068
Impact : Remote Code Execution
Severity : Important
KBs : 4505217, 4505218, 4505219, 4505220, 4505221, 4505222, 4505224, 4505225, 4505419, 4505422
8. Product : ASP.NET
CVEs/Advisory : CVE-2019-1075
Impact : Spoofing
Severity : Moderate
9. Product : Visual Studio
CVEs/Advisory : CVE-2019-1077, CVE-2019-1079, CVE-2019-1113
Impact : Critical
Severity : Elevation of Privilege, Information Disclosure, Remote Code Execution
KBs : 4506161, 4506162, 4506163, 4506164
10. Product : Microsoft Exchange Server
CVEs/Advisory : ADV190021, CVE-2019-1084, CVE-2019-1136, CVE-2019-1137
Impact : Elevation of Privilege, Information Disclosure, Spoofing
Severity : Important
KBs : 4509408, 4509409, 4509410
11. Product : Azure
CVEs/Advisory : CVE-2018-15664
Impact : Elevation of Privilege
Severity : Important
SecPod Saner detects these vulnerabilities and automatically fixes it by applying security updates. Download Saner now and keep your systems updated and secure.