The second Tuesday of April 2026 marked another extensive security update release from Microsoft, addressing a broad range of vulnerabilities across its product ecosystem. This month’s Patch Tuesday resolved a notably high number of security flaws spanning Windows, Microsoft Office, Azure, Edge, SQL Server, Hyper-V, and multiple core Windows components.
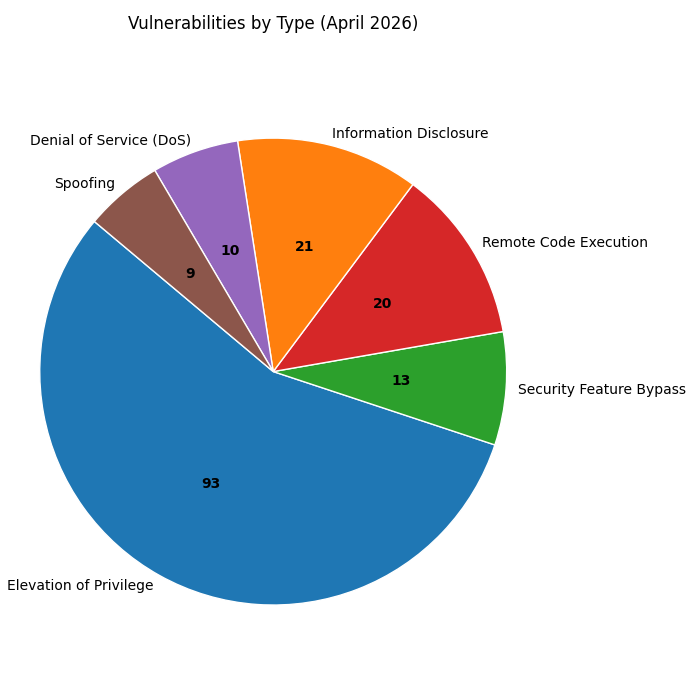
In total, Microsoft patched 167 vulnerabilities, including two zero-day flaws, one of which was confirmed as actively exploited in the wild prior to the release of security updates. The remaining issues span privilege escalation, remote code execution, information disclosure, denial-of-service, and security feature bypass categories, reinforcing the importance of timely patch deployment across enterprise environments.
Summary Overview
Zero-Day Vulnerabilities
Microsoft’s April 2026 Patch Tuesday addressed two zero-day vulnerabilities: one was actively exploited in the wild, and the other was publicly disclosed prior to patch availability. The presence of an exploited SharePoint flaw significantly increases the urgency of this month’s update cycle.
1. CVE-2026-32201 — Microsoft SharePoint Server Spoofing Vulnerability (Actively Exploited)
This actively exploited zero-day vulnerability affects Microsoft SharePoint Server and stems from improper input validation, allowing an unauthenticated attacker to spoof network traffic. According to Microsoft, successful exploitation enables attackers to view sensitive information and modify disclosed data, potentially impacting confidentiality and integrity, though availability is not directly affected.
While Microsoft has not released technical exploitation details or indicators of compromise, confirmation of active exploitation suggests the flaw was already weaponized prior to patch release. In enterprise environments where SharePoint is widely exposed internally or externally, this vulnerability presents a serious risk, particularly when combined with additional weaknesses for lateral movement or data exfiltration. Patches are available for all supported SharePoint versions, and administrators should prioritize deployment without delay.
2. CVE-2026-33825 — Microsoft Defender Elevation of Privilege (Publicly Disclosed)
The second zero-day addressed in April 2026 is a Microsoft Defender Elevation of Privilege vulnerability that allows local attackers to obtain SYSTEM-level privileges. Microsoft confirmed the flaw was publicly disclosed before patching, increasing the likelihood of copycat exploitation following release.
Exploitation of this vulnerability enables attackers to bypass local security boundaries and gain complete control over affected systems, making it particularly dangerous in post-compromise scenarios. Microsoft mitigated the issue through the Microsoft Defender Antimalware Platform update version 4.18.26050.3011, which is automatically delivered to supported systems. However, environments with restricted update mechanisms should verify that the platform update has been successfully applied. The vulnerability was credited to independent security researchers and did not require user interaction to exploit once local access was achieved.
Affected Products
- .NET
- .NET and Visual Studio
- .NET Framework
- .NET, .NET Framework, Visual Studio
- Applocker Filter Driver (applockerfltr.sys)
- Azure Logic Apps
- Azure Monitor Agent
- Desktop Window Manager
- Function Discovery Service (fdwsd.dll)
- GitHub Copilot and Visual Studio Code
- GitHub Repo: Git for Windows
- Input-Output Memory Management Unit (IOMMU)
- Microsoft Brokering File System
- Microsoft Defender
- Microsoft Dynamics 365 (on-premises)
- Microsoft Graphics Component
- Microsoft High Performance Compute Pack (HPC)
- Microsoft Management Console
- Microsoft Office
- Microsoft Office Excel
- Microsoft Office PowerPoint
- Microsoft Office SharePoint
- Microsoft Office Word
- Microsoft Power Apps
- Microsoft PowerShell
- Microsoft Windows
- Microsoft Windows Search Component
- Microsoft Windows Speech
- Node.js
- Remote Desktop Client
- Role: Windows Hyper-V
- SQL Server
- Universal Plug and Play (upnp.dll)
- Windows Active Directory
- Windows Admin Center
- Windows Advanced Rasterization Platform
- Windows Ancillary Function Driver for WinSock
- Windows Biometric Service
- Windows BitLocker
- Windows Boot Loader
- Windows Boot Manager
- Windows Client Side Caching driver (csc.sys)
- Windows Cloud Files Mini Filter Driver
- Windows COM
- Windows Common Log File System Driver
- Windows Container Isolation FS Filter Driver
- Windows Cryptographic Services
- Windows Encrypting File System (EFS)
- Windows File Explorer
- Windows GDI
- Windows Hello
- Windows HTTP.sys
- Windows IKE Extension
- Windows Installer
- Windows Kerberos
- Windows Kernel
- Windows Kernel Memory
- Windows Local Security Authority Subsystem Service (LSASS)
- Windows LUAFV
- Windows Management Services
- Windows OLE
- Windows Print Spooler Components
- Windows Projected File System
- Windows Push Notifications
- Windows Recovery Environment Agent
- Windows Redirected Drive Buffering
- Windows Remote Desktop
- Windows Remote Desktop Licensing Service
- Windows Remote Procedure Call
- Windows RPC API
- Windows Secure Boot
- Windows Sensor Data Service
- Windows Server Update Service
- Windows Shell
- Windows Snipping Tool
- Windows Speech Brokered Api
- Windows SSDP Service
- Windows Storage Spaces Controller
- Windows TCP/IP
- Windows TDI Translation Driver (tdx.sys)
- Windows Universal Plug and Play (UPnP) Device Host
- Windows USB Print Driver
- Windows User Interface Core
- Windows Virtualization-Based Security (VBS) Enclave
- Windows WalletService
- Windows WFP NDIS Lightweight Filter Driver (wfplwfs.sys)
- Windows Win32K – GRFX
- Windows Win32K – ICOMP
Remediation
- Prioritize zero-day and Critical vulnerabilities
Immediately apply patches for the actively exploited SharePoint zero-day (CVE-2026-32201), the Microsoft Defender zero-day (CVE-2026-33825), and all Critical remote code execution vulnerabilities. - Secure SharePoint and collaboration platforms first
Organizations running on-premises SharePoint should patch without delay and review logs for suspicious access or spoofing activity. - Monitor for privilege escalation and post-compromise behavior
Given the high volume of Elevation of Privilege flaws, security teams should closely monitor for abnormal privilege transitions, token abuse, and SYSTEM-level execution. - Patch Office, Remote Desktop, and endpoint systems early
Remote code execution vulnerabilities in Microsoft Office, Remote Desktop Client, and endpoint tools should be remediated quickly to reduce phishing and lateral movement risks. - Ensure consistent patching across cloud, servers, and endpoints
The wide product impact of April’s updates makes uniform patch deployment across endpoints, servers, virtualization, and cloud workloads critical to preventing exploitation chains.
Instantly Fix Risks with Saner Patch Management
Saner patch management is a continuous, automated, and integrated software that instantly fixes risks exploited in the wild. The software supports major operating systems like Windows, Linux, and macOS, as well as 550+ third-party applications.
It also allows you to set up a safe testing area to test patches before deploying them in a primary production environment. Saner patch management additionally supports a patch rollback feature in case of patch failure or a system malfunction.
Experience the fastest and most accurate patching software here.