Threat actors are increasingly moving faster than ever in ransomware operations, shrinking the time between initial compromise and ransomware deployment to maximize impact before defenders can respond. Instead of relying on prolonged persistence, modern ransomware groups are rapidly exploiting newly disclosed vulnerabilities and automating post-compromise actions to accelerate attacks.
According to recent findings from Microsoft Threat Intelligence, the threat actor Storm-1175 has been observed conducting high-speed ransomware campaigns by exploiting newly disclosed vulnerabilities and deploying Medusa ransomware shortly after gaining access. The group has demonstrated the ability to move from initial compromise to ransomware deployment in less than 24 hours in some incidents.
Background on Storm-1175 Operations
Storm-1175 is a financially motivated threat actor known for exploiting internet-facing systems to gain initial access and rapidly deploying ransomware. Microsoft has tracked the group targeting organizations across multiple sectors using aggressive exploitation tactics and fast operational execution.
Storm-1175 operations commonly involve:
- Exploiting vulnerable public-facing applications
- Quickly weaponizing newly disclosed vulnerabilities
- Conducting rapid lateral movement after compromise
- Harvesting credentials and escalating privileges
- Deploying ransomware with minimal dwell time
Microsoft notes that the group’s speed and adaptability make it a significant threat to organizations with exposed or unpatched perimeter systems.
Timeline and Scope
- Threat Actor Activity Tracked Since: 2023
- Ransomware Family Used: Medusa
- Time to Ransomware Deployment: As little as 24 hours
- Targeting Regions: Primarily United States, United Kingdom, and Australia
Infection Method
Storm-1175 gains initial access by exploiting vulnerable internet-facing applications and services. Microsoft observed the group targeting organizations with exposed systems that had not yet been patched against recently disclosed vulnerabilities.
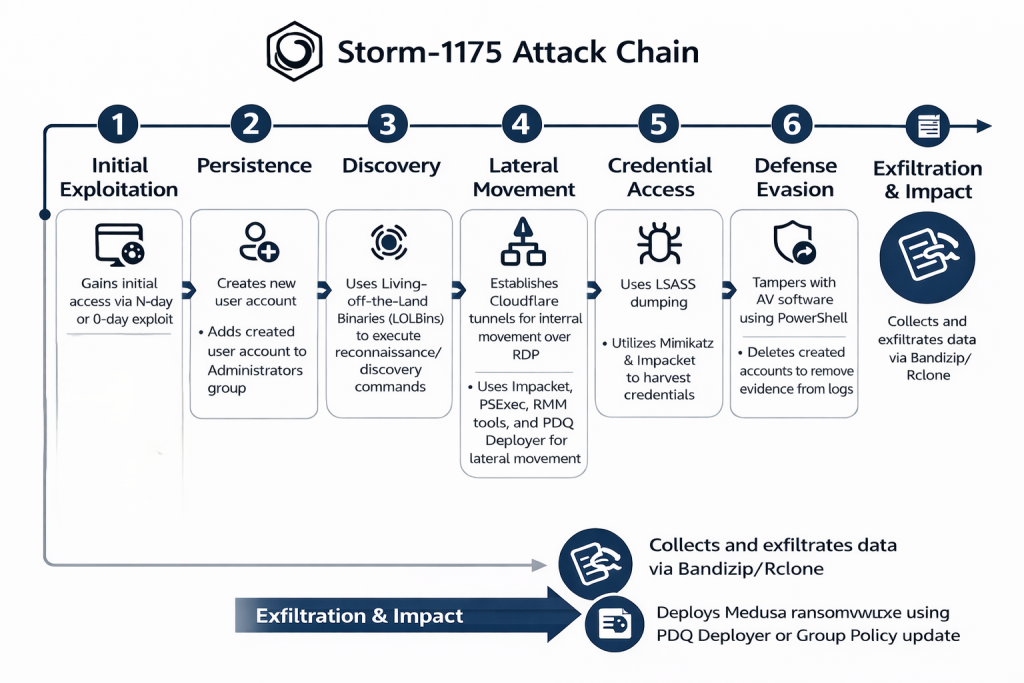
The attackers use tools such as PowerShell, PsExec, and PDQ Deploy to move across the network and weaken defenses by modifying security settings and disabling protections. Once defenses are reduced, Medusa ransomware is deployed across compromised systems.
Exploited Vulnerabilities Observed
Microsoft observed Storm-1175 exploiting vulnerabilities across several enterprise platforms, including flaws in:
| CVE ID | Affected product | CVSS | EPSS |
|---|---|---|---|
| CVE-2026-1731 – OS Command Injection allowing unauthenticated RCE | BeyondTrust | 9.8 (Critical) | 80.06 % |
| CVE-2023-21529 – Deserialization of untrusted data leading to RCE | Microsoft Exchange | 8.8 (High) | 35.02% |
| CVE-2023-27350 – Authentication bypass leading to remote code execution | PaperCut | 9.8 (Critical) | 94.26% |
| CVE-2023-27351 – Authentication bypass vulnerability | PaperCut | 9.8 (Critical) | 44.63% |
| CVE-2023-46805 – Authentication bypass in web component | Ivanti Connect Secure / Policy Secure | 8.2 (High) | 94.37% |
| CVE-2024-21887 – Command injection vulnerability | Ivanti Connect Secure / Policy Secure | 9.1 (Critical) | 94.41% |
| CVE-2024-1709 – Authentication bypass using alternate path | ConnectWise ScreenConnect | 10.0 (Critical) | 94.32% |
| CVE-2024-1708 – Path traversal vulnerability | ConnectWise ScreenConnect | 8.4 (High) | 52.12% |
| CVE-2024-27198 – Authentication bypass allowing admin actions / RCE | JetBrains TeamCity | 9.8 (Critical) | 93.05% |
| CVE-2024-27199– Path traversal authentication bypass | JetBrains TeamCity | 7.3 (High) | 82.47% |
| CVE-2024-57726 – Privilege escalation via excessive API permissions | SimpleHelp | 9.9 (Critical) | 0.30% |
| CVE-2024-57727 – Unauthenticated file download (path traversal) | SimpleHelp | 9.1 (Critical) | 94.02% |
| CVE-2024-57728 – Arbitrary file upload leading to RCE | SimpleHelp | 9.8 (Critical) | 1.03% |
| CVE-2025-31161 – Authentication bypass and admin account takeover | CrushFTP | 9.8 (Critical) | 86.21% |
| CVE-2025-10035 – Deserialization of untrusted data leading to RCE | GoAnywhere MFT | 10.0 (Critical) | 54.64% |
| CVE-2025-52691 – Unrestricted file upload with dangerous type | SmarterMail | 10.0 (Critical) | 87.29% |
| CVE-2026-23760 – Authentication bypass via alternate path | SmarterMail | 9.3 (Critical) | 79.94% |
Indicators of Compromise (IOCs)
- Creation of new local or domain user accounts, followed by addition to the Administrators group.
- Credential dumping from LSASS, using tools such as Impacket and Mimikatz.
- Deployment of web shells or remote access payloads on web facing servers.
MITRE ATT&CK Mapping
- TA0001 – Initial Access: Exploit Public-Facing Application
- TA0002 – Execution: Command and Scripting Interpreter
- TA0003 – Persistence: Create Account / Web Shell
- TA0006 – Credential Access: OS Credential Dumping
- TA0005 – Defense Evasion: Impair Defenses
- TA0008 – Lateral Movement: Remote Services
- TA0040 – Impact: Data Encrypted for Impact
Mitigation
- Patch internet-facing systems immediately after vulnerability disclosure
- Prioritize remediation of exposed perimeter services
- Monitor for suspicious administrative tool usage
- Audit creation of new privileged accounts
- Restrict unnecessary remote management tools
- Enable multi-factor authentication for privileged accounts
- Continuously monitor for credential dumping activity
Instantly Fix Risks with Saner Patch Management
Saner patch management is a continuous, automated, and integrated software that instantly fixes risks exploited in the wild. The software supports major operating systems like Windows, Linux, and macOS, as well as 550+ third-party applications.
It also allows you to set up a safe testing area to test patches before deploying them in a primary production environment. Saner patch management additionally supports a patch rollback feature in case of patch failure or a system malfunction.
Experience the fastest and most accurate patching software here.