The second Tuesday of May 2026 marked another major security update release from Microsoft, addressing a broad range of vulnerabilities across Windows, Microsoft Office, SharePoint, Dynamics 365, .NET, DNS Client, and other core enterprise components. While this month’s Patch Tuesday did not include any actively exploited or publicly disclosed zero-day vulnerabilities, the release still contained a significant number of high-severity flaws that require immediate attention from enterprise security teams.
In total, Microsoft patched 120 vulnerabilities, including 17 classified as Critical. The updates addressed multiple categories of security weaknesses, including remote code execution, elevation of privilege, spoofing, information disclosure, denial of service, and security feature bypass vulnerabilities. Several of the most severe flaws affect widely deployed enterprise services such as Microsoft Office, SharePoint Server, Windows DNS Client, and Microsoft Dynamics 365, reinforcing the importance of timely patch deployment and vulnerability management.
Summary Overview
Security researchers noted that this was the first Patch Tuesday release since June 2024 without a zero-day vulnerability, offering organizations a less urgent—but still highly important—patching cycle compared to recent months.
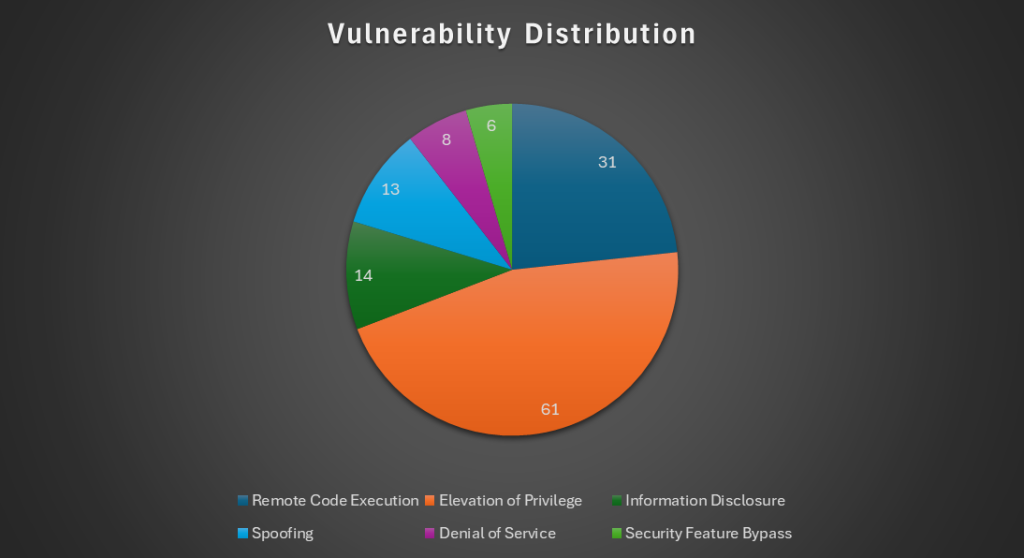
Note that this chart also includes vulnerabilities in Mariner, Azure, Copilot, Microsoft Teams, and Microsoft Partner Center that were addressed earlier this month and are not included in today’s 120 Patch Tuesday fixes.
Notable Vulnerabilities
Although May 2026 did not bring any zero-days with it, Microsoft addressed several high-risk vulnerabilities that could enable remote code execution or significant privilege escalation in enterprise environments.
1. CVE-2026-40365 — Microsoft SharePoint Server Remote Code Execution Vulnerability
Microsoft patched a Remote Code Execution vulnerability affecting Microsoft SharePoint Server that allows an authenticated attacker to execute code remotely over a network. Successful exploitation could allow attackers to compromise SharePoint environments and potentially move laterally across enterprise infrastructure.
Because SharePoint servers frequently store sensitive organizational data and are often integrated with authentication and collaboration services, this vulnerability should be prioritized in patch deployment schedules. Organizations operating on-premises SharePoint environments should apply updates immediately and review systems for suspicious activity.
2. CVE-2026-41096 — Windows DNS Client Remote Code Execution Vulnerability
This vulnerability affects the Windows DNS Client service and can be exploited by a malicious or attacker-controlled DNS server sending specially crafted DNS responses to vulnerable systems. According to reporting, successful exploitation may lead to memory corruption and allow attackers to execute arbitrary code remotely.
Because DNS services are fundamental to enterprise networking operations, exploitation of this flaw could have widespread impact across endpoints and servers. Security teams should prioritize patching internet-facing and business-critical systems first.
3. CVE-2026-35421 — Windows GDI Remote Code Execution Vulnerability
Microsoft also addressed a Windows Graphics Device Interface (GDI) Remote Code Execution vulnerability that can be triggered through malicious Enhanced Metafile (EMF) files opened in Microsoft Paint.
Exploitation requires user interaction, but the flaw presents a phishing and malware delivery risk, particularly in environments where users frequently interact with image attachments or downloaded content.
4. Microsoft Office and Word Remote Code Execution Vulnerabilities
The May 2026 updates also fixed multiple Remote Code Execution vulnerabilities affecting Microsoft Office, Word, and Excel. These flaws can be exploited through specially crafted files and, in some cases, may be triggered through the Preview Pane without fully opening the document.
Given the continued use of malicious Office documents in phishing campaigns, organizations should prioritize Office updates alongside endpoint protection and email security controls.
Affected Products
- .NET
- .NET Framework
- Azure Logic Apps
- Microsoft Dynamics 365 (on-premises)
- Microsoft Office
- Microsoft Office Excel
- Microsoft Office Word
- Microsoft SharePoint Server
- Microsoft Windows
- Windows DNS Client
- Windows GDI
- Windows Netlogon
- Windows Kernel
- Windows Remote Desktop components
- Windows Security Features
- Windows Networking Components
- Windows Graphics Components
- Windows Authentication Services
- Windows Privilege Management Components
Users are urged to patch their systems immediately.
Instantly Fix Risks with Saner Patch Management
Saner patch management is a continuous, automated, and integrated software that instantly fixes risks exploited in the wild. The software supports major operating systems like Windows, Linux, and macOS, as well as 550+ third-party applications.
It also allows you to set up a safe testing area to test patches before deploying them in a primary production environment. Saner patch management additionally supports a patch rollback feature in case of patch failure or a system malfunction.
Experience the fastest and most accurate patching software here.