AUGMENTED REALITY
Augmented Reality is a sort of virtual reality that aims to duplicate the actual world’s environment in a computer. An augmented reality system creates a composite view for the user that is the combination of the real scene viewed by the user and a virtual scene produced by the computer that enhances the scene with additional information on the screen. The virtual scene generated by the processor is designed to enhance the user’s sensory perception of the virtual world they are viewing or interacting with. The objective of Augmented Reality is to create a system in which the user cannot articulate the difference between the existing world and the virtual augmentation of it. Nowadays Augmented Reality is used in military training, robotics, entertainment, manufacturing, engineering design, and other industries.
Wearable technology hasn’t quite made it to mainstream businesses but it will, very soon, and it’s going to change the way people think and the way they do their work, in fact, it makes them easy to understand and improve the efficiency of their work.
The Internet of Things has been heralded as the next wave in mobility and personal computing. But most of the interest to date has centred on consumer use of wearable devices like, google glasses, smartwatches and 3-D head-up displays — devices that let people view the data which they want while looking straight ahead. These are interesting areas of study, as they provide motivation for users to experiment with computer-aided, real-world environments known as Augmented Reality.
Many businesses today are still in the beginning phase with this technology. But very soon, employees will start bringing wearables to work, as they did with smartphones and other gadgets, and start using them for business purposes. But the upcoming change will be much advanced than that. Business establishments will inevitably search for tools that increase the efficiency of their workers and exploit the effectiveness of their resources. Indeed, in the near future, I predict most people will use augmented-reality technology like sensors, head-up displays, even perceptual systems the kind of computing that allows us to control devices without even touching them, or lets the software to adjust to movements captured by video cameras.
So do you get a picture what might an augmented workforce be like?
Imagine having a service technician come to your house to fix your home appliance. He will just point his head-up display at the device or appliance. A camera will capture the model name and then upload it to the company’s cloud. This in turn triggers a download of schematics and instructions, along with a virtual-reality view of the machine’s components present inside the product on his display. Once the problem is diagnosed as a bad component, the tech will upload a computer-aided design of the needed part to a 3-D printer in his truck. By the time he gets back to the truck, the part will be made and ready for installation.
Such tools make every technician sent on a service call an expert and of course the customer’s relationship boosts. That makes for more uniform service through the board, and it involves only one visit, there’s no need to go back, order a part and then return another day to mount it. And with all the sensor data flowing in to the home office, a best-case routing algorithm will be able to realize which technicians have completed service calls assigned and which is nearby to the next one, allowing service teams to help more clients a day.
And finally, with an assets of data to retrieve and analyse, a business organization can increase business insights it couldn’t before, improving service quality and profits and strengthening customer loyalty. For instance, in the home appliance example, the organization may quickly discover which machines have the highest failure level and take suitable action like issue a recall or send out technicians to do proactive maintenance. It can also swiftly judge how well resources such as trucks and storage facilities are being used.
Of course, getting there won’t be that easy. Corporate infrastructures and systems will need to be progressed for performance. And so will the network access and security, back-office applications like ERPs, device management and cloud-based services. It will require increased network bandwidth, more wireless connectivity options and an expanded ability to identify devices and allow access and of course the more important thing security and privacy. Further, transforming interfaces from “point, click and type” to “speak and be heard and view” will involve redesigns of business processes and applications, from what’s seen on tablet or smartphone screens to the workflows and rules programmed into the software.
Does this sound too sci-fi? We’re on the verge of this happening now, with new gadgets like voice and vision-activated computing invading the market. We will soon see an explosion of augmented-reality technology projects upcoming in the next few years in public services, medicines, financial industries. And then there are the “Internet-connected things” we haven’t even seen yet, they’ll have a major influence on the way we work and the way firms do business. The phase to start assembling the high-tech tools, connections and back-office systems for employees of the future is now.
Risks
Organizations are concerned with Augmented Reality attackers, who may integrate trusted content into their malicious Augmented Reality channels, and “ad attackers”, whose malicious content (e.g., online ads, navigators) is incorporated into trusted Augmented Reality channels but confined into iframes
These are few vulnerabilities the researchers have identified the ways the attackers would attack an Augmented Reality Application.
Cross-site scripting.
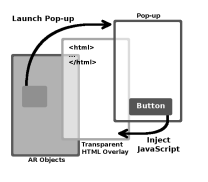
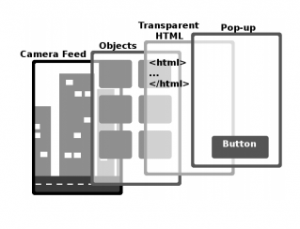 The XML definition of an Augmented Reality object in an application can have a popup field with a textual description and an array of buttons. When that object is clicked, a partly transparent window with the pop-up’s description and buttons is opened on top of the transparent overlay. Each button or objects contains either a URL, or JavaScript code. When a button is clicked, the connected URL is loaded in an opaque window. If the button contains JavaScript, it is executed in the transparent overlay even if the origin of the content in the overlay is different from the origin of the channel that provided the script. This setup opens a hole in the same-origin policy. A malicious channel can specify any origin for the transparent page and associate an arbitrary script with a button. When the button is clicked, this script is injected into the transparent page and gains unrestricted access to all content from this page’s origin.
The XML definition of an Augmented Reality object in an application can have a popup field with a textual description and an array of buttons. When that object is clicked, a partly transparent window with the pop-up’s description and buttons is opened on top of the transparent overlay. Each button or objects contains either a URL, or JavaScript code. When a button is clicked, the connected URL is loaded in an opaque window. If the button contains JavaScript, it is executed in the transparent overlay even if the origin of the content in the overlay is different from the origin of the channel that provided the script. This setup opens a hole in the same-origin policy. A malicious channel can specify any origin for the transparent page and associate an arbitrary script with a button. When the button is clicked, this script is injected into the transparent page and gains unrestricted access to all content from this page’s origin.
This cross-site scripting (XSS) vulnerability can be exploited, for example, to modify the victim’s DOM or steal cookies. HtmlDrawable objects in Wikitude (augmented reality SDK is a software development tools or library for location based AR) includes an even simpler XSS vulnerability. A malicious channel can specify any URL for an HtmlDrawable object and use evalJavaScript to inject an arbitrary script into this object.
Universal cross-site scripting.
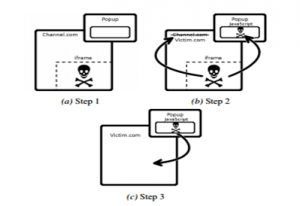
The previously mentioned XSS attacks adopt that the channel is malicious. Regrettably, even if the channel itself is compassionate, all untrusted, third-party content, like online ads, is correctly confined to iframes, and the embedded Web browser which runs the channel’s HTML correctly enforces the SOP, a confined third-party content in the application can perform XSS attacks against any origin of its selection. Consider an application channel that includes an Augmented Reality object with a popup button and suppose that the channel’s transparent HTML page contains an ad in an iframe (Fig. a).
Malicious JavaScript hidden in such an ad can use Augmented RealityEL commands to change the script associated with the popup, and change the URL of the transparent overlay to the victim page (Fig. b). When the button is clicked, the attack script is executed in the victim page (Fig. c). This is a universal XSS vulnerability: a mischievous ad can introduce an arbitrary script into any origin whatsoever.
How to do it right
Quick patches.
The cross-site scripting vulnerabilities described above are caused in part by the fact that the origin of HTML incorporated into an Augmented Reality channel may be different from the channel’s own origin. One reasonable defences is for the Augmented Reality browser to make sure that the two origins are the same; another is to disinfect XML so that it does not contain scripts, which is a notoriously difficult problem. Both defences necessitate the Augmented Reality browser to carefully reason about the origins of content specified in custom XML definitions, thus replicating a complex piece of Web-browser functionality. Furthermore, both defences disable important useful features of Augmented Reality browsers (such as controlling the appearance of Augmented Reality objects from another origin) and may break existing applications. In Wikitude, where evalJavaScript allows channels to inject scripts into an HtmlDrawable regardless of its origin, restricting the origin is not realistic because HtmlDrawable is intended to display content from origins other than the channel itself.
Principled solutions
The root cause of many security holes described in this section is that Augmented Reality objects cannot be described in HTML, thus Augmented Reality browsers must use custom mechanisms to enable HTML content to control these objects. Standardizing Augmented Reality object description languages, including them in HTML5 via either tags, or a special document type, (e.g., channel), and adding support for these new HTML5 features into browsers would allow Augmented Reality content to execute entirely within WebView, eliminating the need for XML and some of the ad-hoc browser interfaces. Unfortunately, assigning origins to these tags is not trivial. In the existing Augmented Reality browsers, all Augmented Reality objects are treated as if their origin is the domain where the main Augmented Reality channel is hosted. Since these objects may contain JavaScript, this is extremely dangerous. The alternative is to extend the same-origin policy to Augmented Reality tags. These tags are intended to support 3D models, animations, UI elements, etc. which may come from different domains but are intended to work smoothly together to produce a unified Augmented Reality experience. A naive extension of the SOP would isolate the Augmented Reality HTML tags based on their domains, but this would prevent them from communicating. The developers would then have to implement cross-origin communication mechanisms, which is fraught with peril. Enforcement of the SOP is complicated further by the fact that several of these new tags may need plugins to be rendered (similar to Flash). Lacking HTML5 support for Augmented Reality, WebView can at least provide origin-restricted APIs that render arbitrary objects on top of camera images and let JavaScript inside WebView control these objects.
References:
t-immersion.com
webopedia.com
Security and Privacy of Augmented Reality Browsers – by Suman Jana University of Texas at Austin