Computers are alive and talking and exchanging ideas and walking around and driving cars and writing poems but, yeah that’s a big BUT, how secure are they while moving so forward? One dropped detail in this big exploration can lead to catastrophe.
The hot deal among tech giants today is a virtual private assistant, from Amazon’s Alexa to Google Assistant to Apple’s Siri to Microsoft’s Cortana all hoarding features in a race to dominate the market.
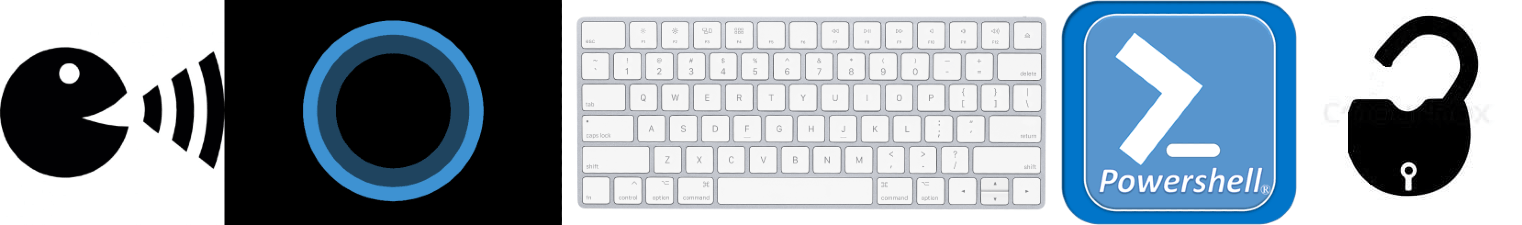
A new vulnerability found in Microsoft’s Cortana lets anyone with physical access to your Windows 10 PC unlock it and takeover by executing PowerShell scripts. Cortana leaves PC being vulnerable, all one has to do is invoke Cortana on the lock screen and start typing as it starts to listen to a query and a Windows contextual menu will appear :
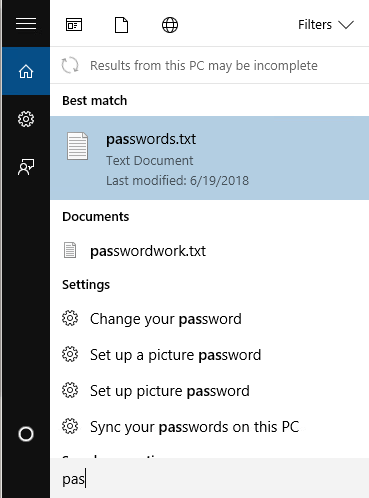
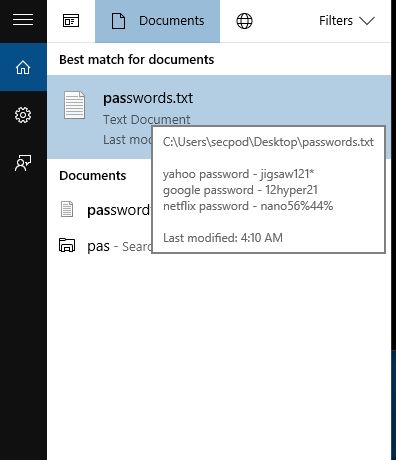
As the string “pas” was typed as soon as Cortana starts to listen, the results are displayed on the lock screen. You can hover over the text files to display the contents of the files on screen :
As you click any one of them, they’ll be opened under the lock screen so you won’t be able to see it. But that’s a good enough reason to explore more. What if an executable or a PowerShell file is clicked on, will they get executed?
So, to list the files on this contextual menu there is a prerequisite, the files should be listed in the Windows indexing. And how to get there?
Well, one-way routes through OneDrive, OneDrive files are indexed by default, so if you share folder or file edit rights with someone, ze can drop a file and it will be indexed. The other way is to insert a USB stick and execute a PowerShell script to get in the USB drive to run the executable. But that’s the whole story? How to? What now? Okay, one process at a time, let’s get on with the OneDrive. It’s simple, it directly appears in the results and once it appears in the results just click to execute and own the system and go berserk and dance … Just one thing, remember those windows in Windows asking for permission to execute a program? Yeah right, you’ll invoke that. You might still be lucky if the user proceeds after unlocking the system.
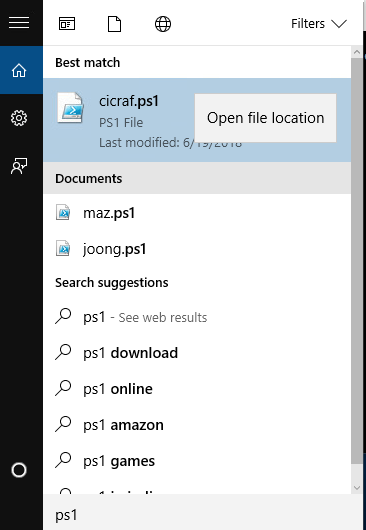
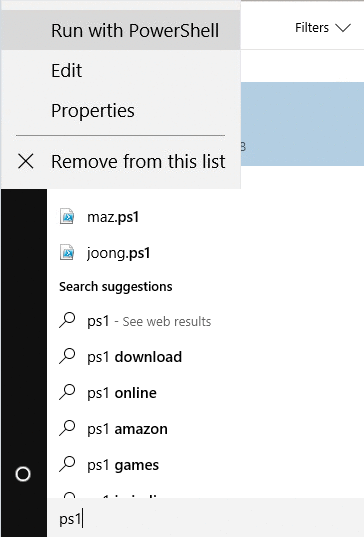
That’s a good scenario but not good enough to satisfy the craving. The next thing is a PowerShell script, What if I click on a PowerShell script and it goes and runs the executable? Well, Microsoft has pretty smart people working for it and they figured this somewhat out. When you click on a PowerShell script, it opens up on a Notepad! yeah, so we can’t execute the script. Aarghh!! this is a horrible blow .. Now what? Try and try.
Well, to execute a PowerShell script, if you have Administrator privileges, it just works, no questions asked. And how to get the privilege? Just right-click and run as Administrator, wow, simple, hacked, woohoo … Oh, snap where is my Run as Administrator button? Furious. This is it. We’re not letting this go.
And then we noticed something, some files in some searches do show the Run as Administrator button. So what’s different with our file? Then we noticed something, earlier in the process, we opened a text file, remember? yeah, that’s showing Run as Administrator button, now should we try this? Okay, let’s rest our nerves there’ve been a lot of rounds of dopamine releases ending up in crap. So let’s get to this, we open the PowerShell file and search it again and do the click, Oh geez nerves! an accidental left click, okay, okay, calm, let’s go again, right-click and yeah, we got this, Run as Administrator and the script executes swiftly.
The Process:
Solution:
To mitigate the issue Microsoft released the patch for the vulnerability (CVE-2018-8140) on 12 June, 2018 with its monthy security releases.
Workaround:
As a workaround, disable Cortana until the patch gets applied.
SecPod Saner detects these vulnerabilities and automatically fixes it by applying security updates. Download Saner now and keep your systems updated and secure.